- What is Cryptography? – An Introduction to Cryptographic Algorithms
- Steganography Tutorial – A Complete Guide For Beginners
- Application Security: All You Need To Know
- What is Computer Security and Its Types
- Penetration Testing – Methodologies and Tools
- What is Network Security? – Fundamentals, Types, Advantages
Cyber Security is the only domain in IT which has not faced a recession yet. With demand, there is also competition, and to get a job in Cybersecurity, you need to be one of the best. While having the necessary Cybersecurity skills is half job done, cracking the interview is another chapter altogether. To help you crack the Cyber security interview, we’ve compiled this list of top Cyber Security interview questions and answers.
This Cybersecurity Interview Questions blog is divided into five parts: Part A – Theoretical Cybersecurity Interview Questions, Part B – Scenario Based Cybersecurity Interview Questions, Part C – Interview Questions for Beginners, Part D – Interview Questions for Intermediates and Part E – Interview Questions for Experienced.
Ready to take your career in cybersecurity to the next level? CISSP Certification is the way!
Let’s get started with
Part A-Theoretical Cyber Security Interview Questions
1. What is Cryptography?
Cryptography is the practice and study of techniques for securing information and communication mainly to protect the data from third parties that the data is not intended for.
2. What is the difference between Symmetric and Asymmetric encryption?
| Basis of Comparison | Symmetric Encryption | Asymmetric Encryption |
| Encryption key | Same key for encryption & decryption | Different keys for encryption & decryption |
| Performance | Encryption is fast but more vulnerable | Encryption is slow due to high computation |
| Algorithms | DES, 3DES, AES and RC4 | Diffie-Hellman, RSA |
| Purpose | Used for bulk data transmission | Often used for securely exchanging secret keys |
3. What is the difference between IDS and IPS?
IDS is Intrusion Detection System and it only detects intrusions and the administrator has to take care of preventing the intrusion. Whereas, in IPS i.e., Intrusion Prevention System, the system detects the intrusion and also takes actions to prevent the intrusion.
4. Explain CIA triad.
CIA stands for Confidentiality, Integrity, and Availability. CIA is a model that is designed to guide policies for Information Security. It is one of the most popular models used by organizations.
Confidentiality
The information should be accessible and readable only to authorized personnel. It should not be accessible by unauthorized personnel. The information should be strongly encrypted just in case someone uses hacking to access the data so that even if the data is accessed, it is not readable or understandable.
Integrity
Making sure the data has not been modified by an unauthorized entity. Integrity ensures that data is not corrupted or modified by unauthorized personnel. If an authorized individual/system is trying to modify the data and the modification wasn’t successful, then the data should be reversed back and should not be corrupted.
Availability
The data should be available to the user whenever the user requires it. Maintaining of Hardware, upgrading regularly, Data Backups and Recovery, Network Bottlenecks should be taken care of.
5. How is Encryption different from Hashing?
Both Encryption and Hashing are used to convert readable data into an unreadable format. The difference is that the encrypted data can be converted back to original data by the process of decryption but the hashed data cannot be converted back to original data.
6. What is a Firewall and why is it used?
A Firewall is a network security system set on the boundaries of the system/network that monitors and controls network traffic. Firewalls are mainly used to protect the system/network from viruses, worms, malware, etc. Firewalls can also be to prevent remote access and content filtering.
Cybersecurity Interview Questions and Answers
This Edureka Cybersecurity Interview Questions and Answers will help you in preparation for your interviews.
7. What is the difference between VA(Vulnerability Assessment) and PT(Penetration Testing)?
Vulnerability Assessment is the process of finding flaws on the target. Here, the organization knows that their system/network has flaws or weaknesses and want to find these flaws and prioritize the flaws for fixing.
Penetration Testing is the process of finding vulnerabilities on the target. In this case, the organization would have set up all the security measures they could think of and would want to test if there is any other way that their system/network can be hacked.
8. What is a three-way handshake?
A three-way handshake is a method used in a TCP/IP network to create a connection between a host and a client. It’s called a three-way handshake because it is a three-step method in which the client and server exchanges packets. The three steps are as follows:
- The client sends a SYN(Synchronize) packet to the server check if the server is up or has open ports
- The server sends SYN-ACK packet to the client if it has open ports
- The client acknowledges this and sends an ACK(Acknowledgment) packet back to the server
9. What are the response codes that can be received from a Web Application?
1xx – Informational responses
2xx – Success
3xx – Redirection
4xx – Client-side error
5xx – Server-side error
Let us now go ahead and take a look at some of the other Cybersecurity Interview Questions
Related Question Best practices for securing HTML forms from XSS attacks
10. What is traceroute? Why is it used?
Traceroute is a tool that shows the path of a packet. It lists all the points (mainly routers) that the packet passes through. This is used mostly when the packet is not reaching its destination. Traceroute is used to check where the connection stops or breaks to identify the point of failure.
11. What is the difference between HIDS and NIDS?
HIDS(Host IDS) and NIDS(Network IDS) are both Intrusion Detection System and work for the same purpose i.e., to detect the intrusions. The only difference is that the HIDS is set up on a particular host/device. It monitors the traffic of a particular device and suspicious system activities. On the other hand, NIDS is set up on a network. It monitors traffic of all device of the network.
12. What are the steps to set up a firewall?
Following are the steps to set up a firewall:
- Username/password: modify the default password for a firewall device
- Remote administration: Disable the feature of the remote administration
- Port forwarding: Configure appropriate port forwarding for certain applications to work properly, such as a web server or FTP server
- DHCP server: Installing a firewall on a network with an existing DHCP server will cause conflict unless the firewall’s DHCP is disabled
- Logging: To troubleshoot firewall issues or potential attacks, ensure that logging is enabled and understand how to view logs
- Policies: You should have solid security policies in place and make sure that the firewall is configured to enforce those policies.
13. Explain SSL Encryption
SSL(Secure Sockets Layer) is the industry-standard security technology creating encrypted connections between Web Server and a Browser. This is used to maintain data privacy and to protect the information in online transactions. The steps for establishing an SSL connection is as follows:
- A browser tries to connect to the webserver secured with SSL
- The browser sends a copy of its SSL certificate to the browser
- The browser checks if the SSL certificate is trustworthy or not. If it is trustworthy, then the browser sends a message to the web server requesting to establish an encrypted connection
- The web server sends an acknowledgment to start an SSL encrypted connection
- SSL encrypted communication takes place between the browser and the web server
14. What steps will you take to secure a server?
Secure servers use the Secure Sockets Layer (SSL) protocol for data encryption and decryption to protect data from unauthorized interception.
Here are four simple ways to secure server:
Step 1: Make sure you have a secure password for your root and administrator users
Step 2: The next thing you need to do is make new users on your system. These will be the users you use to manage the system
Step 3: Remove remote access from the default root/administrator accounts
Step 4: The next step is to configure your firewall rules for remote access
15. Explain Data Leakage
Data Leakage is an intentional or unintentional transmission of data from within the organization to an external unauthorized destination. It is the disclosure of confidential information to an unauthorized entity. Data Leakage can be divided into 3 categories based on how it happens:
- Accidental Breach: An entity unintentionally send data to an unauthorized person due to a fault or a blunder
- Intentional Breach: The authorized entity sends data to an unauthorized entity on purpose
- System Hack: Hacking techniques are used to cause data leakage
Data Leakage can be prevented by using tools, software, and strategies known as DLP(Data Leakage Prevention) Tools.
16. What are some of the common Cyberattacks?
Following are some common cyber attacks that could adversely affect your system.
- Malware
- Phishing
- Password Attacks
- DDoS
- Man in the Middle
- Drive-By Downloads
- Malvertising
- Rogue Software

17. What is a Brute Force Attack? How can you prevent it?
Brute Force is a way of finding out the right credentials by repetitively trying all the permutations and combinations of possible credentials. In most cases, brute force attacks are automated where the tool/software automatically tries to login with a list of credentials. There are various ways to prevent Brute Force attacks. Some of them are:
- Password Length: You can set a minimum length for password. The lengthier the password, the harder it is to find.
- Password Complexity: Including different formats of characters in the password makes brute force attacks harder. Using alpha-numeric passwords along with special characters, and upper and lower case characters increase the password complexity making it difficult to be cracked.
- Limiting Login Attempts: Set a limit on login failures. For example, you can set the limit on login failures as 3. So, when there are 3 consecutive login failures, restrict the user from logging in for some time, or send an Email or OTP to use to log in the next time. Because brute force is an automated process, limiting login attempts will break the brute force process.
Related post : Incident Responder Interview Questions and Answers
18. What is Port Scanning?
Port Scanning is the technique used to identify open ports and service available on a host. Hackers use port scanning to find information that can be helpful to exploit vulnerabilities. Administrators use Port Scanning to verify the security policies of the network. Some of the common Port Scanning Techniques are:
- Ping Scan
- TCP Half-Open
- TCP Connect
- UDP
- Stealth Scanning
Enroll in a prestigious Cyber Security Internship program to kickstart your career.
19. What are the different layers of the OSI model?
An OSI model is a reference model for how applications communicate over a network. The purpose of an OSI reference is to guide vendors and developers so the digital communication products and software programs can interoperate.
Following are the OSI layers: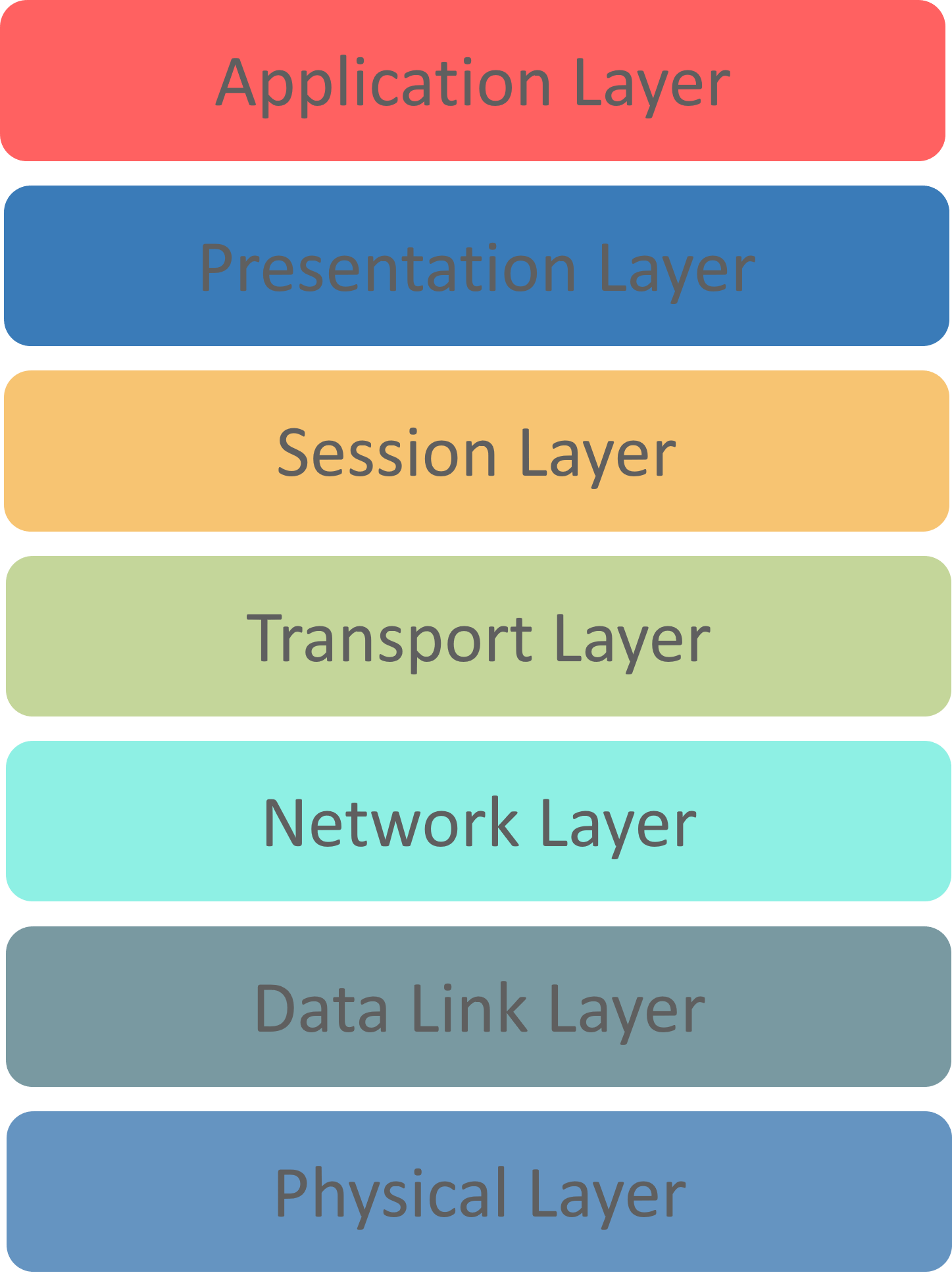
Physical Layer: Responsible for transmission of digital data from sender to receiver through the communication media,
Data Link Layer: Handles the movement of data to and from the physical link. It is also responsible for encoding and decoding of data bits.
Network Layer: Responsible for packet forwarding and providing routing paths for network communication.
Transport Layer: Responsible for end-to-end communication over the network. It splits the data from the above layer and passes it to the Network Layer and then ensures that all the data has successfully reached at the receiver’s end.
Session Layer: Controls connection between the sender and the receiver. It is responsible for starting, ending, and managing the session and establishing, maintaining and synchronizing interaction between the sender and the receiver.
Presentation Layer: It deals with presenting the data in a proper format and data structure instead of sending raw datagrams or packets.
Application Layer: It provides an interface between the application and the network. It focuses on process-to-process communication and provides a communication interface.
20. What is a VPN?
Almost all Cybersecurity Interview Questions will have this question included. VPN stands for Virtual Private Network. It is used to create a safe and encrypted connection. When you use a VPN, the data from the client is sent to a point in the VPN where it is encrypted and then sent through the internet to another point. At this point, the data is decrypted and sent to the server. When the server sends a response, the response is sent to a point in the VPN where it is encrypted and this encrypted data is sent to another point in the VPN where it is decrypted. And finally, the decrypted data is sent to the client. The whole point of using a VPN is to ensure encrypted data transfer.
21. What do you understand by Risk, Vulnerability & Threat in a network?
Threat: Someone with the potential to harm a system or an organization
Vulnerability: Weakness in a system that can be exploited by a potential hacker
Risk: Potential for loss or damage when threat exploits a vulnerability
22. How can identity theft be prevented?
Here’s what you can do to prevent identity theft:
-
- Ensure strong and unique password
- Avoid sharing confidential information online, especially on social media
- Shop from known and trusted websites
- Use the latest version of the browsers
- Install advanced malware and spyware tools
- Use specialized security solutions against financial data
- Always update your system and the software
- Protect your SSN (Social Security Number)
23. What are black hat, white hat and grey hat hackers?
Black hat hackers are known for having vast knowledge about breaking into computer networks. They can write malware which can be used to gain access to these systems. This type of hackers misuse their skills to steal information or use the hacked system for malicious purpose.
White hat hackers use their powers for good deeds and so they are also called Ethical Hackers. They are hired by companies to identify and fix vulnerabilities in systems to improve security. Check out our Certified Ethical Hacking Course: CEH v13 AI program to learn more about ethical hacking.
Anonymity is just a simple thing in Ethical Hacking & CyberSecurity. If you are interested in this domain, check Edureka’s CompTIA Security+ Certification Training.
Grey hat hackers are an amalgamation of a white hat and black hat hacker. They look for system vulnerabilities without the owner’s permission. If they find any vulnerabilities, they report it to the owner. Unlike Black hat hackers, they do not exploit the vulnerabilities found.
24. How often should you perform Patch management?
Patch management should be done as soon as it is released. For windows, once the patch is released it should be applied to all machines, not later than one month. Same goes for network devices, patch it as soon as it is released. Proper patch management should be followed.
25. How would you reset a password-protected BIOS configuration?
Since BIOS is a pre-boot system it has its own storage mechanism for settings and preferences. A simple way to reset is by popping out the CMOS battery so that the memory storing the settings lose its power supply and as a result, it will lose its setting.
26. Explain MITM attack and how to prevent it?
A MITM(Man-in-the-Middle) attack is a type of attack where the hacker places himself in between the communication of two parties and steal the information. Suppose there are two parties A and B having a communication. Then the hacker joins this communication. He impersonates as party B to A and impersonates as party A in front of B. The data from both the parties are sent to the hacker and the hacker redirects the data to the destination party after stealing the data required. While the two parties think that they are communicating with each other, in reality, they are communicating with the hacker.
You can prevent MITM attack by using the following practices:
- Use VPN
- Use strong WEP/WPA encryption
- Use Intrusion Detection Systems
- Force HTTPS
- Public Key Pair Based Authentication
27. Explain DDOS attack and how to prevent it?
This again is an important Cybersecurity Interview Question. A DDOS(Distributed Denial of Service) attack is a cyberattack that causes the servers to refuse to provide services to genuine clients. DDOS attack can be classified into two types:
- Flooding attacks: In this type, the hacker sends a huge amount of traffic to the server which the server can not handle. And hence, the server stops functioning. This type of attack is usually executed by using automated programs that continuously send packets to the server.
- Crash attacks: In this type, the hackers exploit a bug on the server resulting in the system to crash and hence the server is not able to provide service to the clients.
You can prevent DDOS attacks by using the following practices:
- Use Anti-DDOS services
- Configure Firewalls and Routers
- Use Front-End Hardware
- Use Load Balancing
- Handle Spikes in Traffic
28. Explain XSS attack and how to prevent it?
XSS(Cross-Site Scripting) is a cyberattack that enables hackers to inject malicious client-side scripts into web pages. XSS can be used to hijack sessions and steal cookies, modify DOM, remote code execution, crash the server etc.
You can prevent XSS attacks by using the following practices:
- Validate user inputs
- Sanitize user inputs
- Encode special characters
- Use Anti-XSS services/tools
- Use XSS HTML Filter
29. What is an ARP and how does it work?
Address Resolution Protocol (ARP)is a protocol for mapping an Internet Protocol address (IP address) to a physical machine address that is recognized in the local network.
When an incoming packet destined for a host machine on a particular local area network arrives at a gateway, the gateway asks the ARP program to find a physical host or MAC address that matches the IP address.
The ARP program looks in the ARP cache and, if it finds the address, provides it so that the packet can be converted to the right packet length and format and sent to the machine.
If no entry is found for the IP address, ARP broadcasts a request packet in a special format to all the machines on the LAN to see if one machine knows that it has that IP address associated with it.
30. What is port blocking within LAN?
Restricting the users from accessing a set of services within the local area network is called port blocking.
Stopping the source to not to access the destination node via ports. As the application works on the ports, so ports are blocked to restricts the access filling up the security holes in the network infrastructure.
31. What protocols fall under TCP/IP internet layer?
| TCP/IP | TCP/IP Protocol Examples |
| Application | NFS, NIS+, DNS, telnet, ftp, rlogin, rsh, rcp, RIP, RDISC, SNMP and others |
| Transport | TCP, UDP |
| Internet | IP, ARP, ICMP |
| Data Link | PPP, IEEE 802.2 |
| Physical Network | Ethernet (IEEE 802.3) Token ring, RS-232, others |
32. What is a Botnet?
A Botnet is a number of devices connected to the internet where each device has one or more bots running on it. The bots on the devices and malicious scripts used to hack a victim. Botnets can be used to steal data, send spams and execute a DDOS attack.
33. What are salted hashes?
Salt is a random data. When a properly protected password system receives a new password, it creates a hash value of that password, a random salt value, and then the combined value is stored in its database. This helps to defend against dictionary attacks and known hash attacks.
Example: If someone uses the same password on two different systems and they are being used using the same hashing algorithm, the hash value would be same, however, if even one of the system uses salt with the hashes, the value will be different.
34. Explain SSL and TLS
SSL is meant to verify the sender’s identity but it doesn’t search for anything more than that. SSL can help you track the person you are talking to but that can also be tricked at times.
TLS is also an identification tool just like SSL, but it offers better security features. It provides additional protection to the data and hence SSL and TLS are often used together for better protection.
35. What is data protection in transit vs data protection at rest?
| Data Protection in transit | Data protection at rest |
| When data is going from server to client | When data just exists in its database or on its hard drive |
| Effective Data protection measures for in-transit data are critical as data is less secure when in motion | Data at rest is sometimes considered to be less vulnerable than data in transit |
36. What is 2FA and how can it be implemented for public websites?
An extra layer of security that is known as “multi-factor authentication“.
Requires not only a password and username but also something that only, and only, that user has on them, i.e. a piece of information only they should know or have immediately to hand – such as a physical token.
Authenticator apps replace the need to obtain a verification code via text, voice call or email.
37. What is Cognitive Cybersecurity?
Cognitive Cybersecurity is an application of AI technologies patterned on human thought processes to detect threats and protect physical and digital systems.
Self-learning security systems use data mining, pattern recognition, and natural language processing to simulate the human brain, albeit in a high-powered computer model.
38. What is the difference between VPN and VLAN?
| VPN | VLAN |
| Helps to group workstations that are not within the same locations into the same broadcast domain | Related to remote access to the network of a company |
| Means to logically segregate networks without physically segregating them with various switches | Used to connect two points in a secured and encrypted tunnel |
| Saves the data from prying eyes while in transit and no one on the net can capture the packets and read the data | Does not involve any encryption technique but it is only used to slice up your logical network into different sections for the purpose of management and security |
39. Explain Phishing and how to prevent it?
Phishing is a Cyberattack in which a hacker disguises as a trustworthy person or business and attempt to steal sensitive financial or personal information through fraudulent email or instant message.
You can prevent Phishing attacks by using the following practices:
- Don’t enter sensitive information in the webpages that you don’t trust
- Verify the site’s security
- Use Firewalls
- Use AntiVirus Software that has Internet Security
- Use Anti-Phishing Toolbar
40. Explain SQL Injection and how to prevent it?
SQL Injection (SQLi) is a code injection attack where an attacker manipulates the data being sent to the server to execute malicious SQL statements to control a web application’s database server, thereby accessing, modifying and deleting unauthorized data. This attack is mainly used to take over database servers.
You can prevent SQL Injection attacks by using the following practices:
- Use prepared statements
- Use Stored Procedures
- Validate user input
This brings us to the end of Theory Based Cybersecurity Interview Questions
Top 10 Technologies To Learn In 2025
Part B – Scenario Based CybersecCyber security Interview Questions
1. Here’s a situation- You receive the following email from the help desk:
Dear XYZ Email user,
To create space for more users we’re deleting all inactive email accounts. Here’s what you have to send to save your account from getting deleted:
- Name (first and last):
- Email Login:
- Password:
- Date of birth:
- Alternate email
If we don’t receive the above information from you by the end of the week, your email account will be terminated.
If you’re a user what do you do? Justify your answer.
This email is a classic example of “phishing” – trying to trick you into “biting”. The justification is the generalized way of addressing the receiver which is used in mass spam emails.
Above that, a corporate company will never ask for personal details on mail.
They want your information. Don’t respond to email, instant messages (IM), texts, phone calls, etc., asking you for your password or other private information.
You should never disclose your password to anyone, even if they say they work for UCSC, ITS, or other campus organizations.
2. A friend of yours sends an e-card to your mail. You have to click on the attachment to get the card.
What do you do? Justify your answer
There are four risks here:
- Some attachments contain viruses or other malicious programs, so just in general, it’s risky to open unknown or unsolicited attachments.
- Also, in some cases just clicking on a malicious link can infect a computer, so unless you are sure a link is safe, don’t click on it.
- Email addresses can be faked, so just because the email says it is from someone you know, you can’t be certain of this without checking with the person.
- Finally, some websites and links look legitimate, but they’re really hoaxes designed to steal your information.
3. One of the staff members in XYZ subscribes to many free magazines. Now, to activate her subscriptions one of the magazines asked for her month of birth, second asked for her year of birth, the other one asked for her maiden name.
What do you infer from this situation? Justify.
All three newsletters probably have the same parent company or are distributed through the same service. The parent company or service can combine individual pieces of seemingly-harmless information and use or sell it for identity theft
It is even possible that there is a fourth newsletter that asks for a day of birth as one of the activation questions
Often questions about personal information are optional. In addition to being suspicious about situations like the one described here, never provide personal information when it is not legitimately necessary, or to people or companies, you don’t personally know.
4. In our computing labs, print billing is often tied to the user’s login. Sometimes people call to complain about bills for printing they never did only to find out that the bills are, indeed, correct.
What do you infer from this situation? Justify.
Sometimes they realize they loaned their account to a friend who couldn’t remember his/her password, and the friend did the printing. Thus the charges. It’s also possible that somebody came in behind them and used their account
This is an issue with shared or public computers in general. If you don’t log out of the computer properly when you leave, someone else can come in behind you and retrieve what you were doing, use your accounts, etc. Always log out of all accounts, quit programs, and close browser windows before you walk away.
5. There is this case that happened in my computer lab. A friend of mine used their yahoo account at a computer lab on campus. She ensured that her account was not left open before she left the lab. Someone came after her and used the same browser to re-access her account. and they started sending emails from it.
What do you think might be going on here?
The first person probably didn’t log out of her account, so the new person could just go to history and access her account.
Another possibility is that she did log out, but didn’t clear her web cache. (This is done through the browser menu to clear pages that the browser has saved for future use.)
6. Two different offices on campus are working to straighten out an error in an employee’s bank account due to a direct deposit mistake.
Office #1 emails the correct account and deposit information to office #2, which promptly fixes the problem.
The employee confirms with the bank that everything has, indeed, been straightened out.
What is wrong here?
Account and deposit information is sensitive data that could be used for identity theft. Sending this or any kind of sensitive information by email is very risky because email is typically not private or secure. Anyone who knows how can access it anywhere along its route.
As an alternative, the two offices could have called each other or worked with ITS to send the information a more secure way.
7. The mouse on your computer screen starts to move around on its own and click on things on your desktop. What do you do?
a) Call your co-workers over so they can see
b) Disconnect your computer from the network
c) Unplug your mouse
d) Tell your supervisor
e) Turn your computer off
f) Run anti-virus
g) All of the above
Select all the options that apply.
Right answer is B & D.
This is definitely suspicious. Immediately report the problem to your supervisor and the ITS Support Center: itrequest.ucsc.edu, 459-HELP (4357), help@ucsc.edu or Kerr Hall room 54, M-F 8AM-5PM
Also, since it seems possible that someone is controlling the computer remotely, it is best if you can disconnect the computer from the network (and turn off wireless if you have it) until help arrives. If possible, don’t turn off the computer.
8. Below is a list of passwords pulled out a database.
A. @#$)*&^%
B. akHGksmLN
C.UcSc4Evr!
D.Password1
Which of the following passwords meets UCSC’s password requirements?
Answer is UcSc4Evr!
This is the only choice that meets all of the following UCSC requirements:
At least 8 characters in length
Contains at least 3 of the following 4 types of characters: lower case letters, upper case letters, numbers, special characters
Not a word preceded or followed by a digit
9. You receive an email from your bank telling you there is a problem with your account. The email provides instructions and a link so you can log into your account and fix the problem.
What should you do?
Delete the email. Better yet, use the web client (e.g. gmail, yahoo mail, etc.) and report it as spam or phishing, then delete it.
Any unsolicited email or phone call asking you to enter your account information, disclose your password, financial account information, social security number, or other personal or private information is suspicious – even if it appears to be from a company you are familiar with. Always contact the sender using a method you know is legitimate to verify that the message is from them.
10. A while back, the IT folks got a number of complaints that one of our campus computers was sending out Viagra spam. They checked it out, and the reports were true: a hacker had installed a program on the computer that made it automatically send out tons of spam email without the computer owner’s knowledge.
How do you think the hacker got into the computer to set this up?
This was actually the result of a hacked password. Using passwords that can’t be easily guessed, and protecting your passwords by not sharing them or writing them down can help to prevent this. Passwords should be at least 8 characters in length and use a mixture of upper and lower case letters, numbers, and symbols.
Even though in this case it was a hacked password, other things that could possibly lead to this are:
- Out of date patches/updates
- No anti-virus software or out of date anti-virus software
“Part C – Cybersecurity Interview Questions for Beginners
1. What is Cybersecurity, and why is it important?
The critical importance of cybersecurity is mainly to protect computer systems, networks, and programs from cyber-attacks whose aim is access, alter, or destroy sensitive user data. In this case, it also helps in ensuring confidentiality of information, as well as preventing privacy breaches or financial losses.
2 . Define the terms virus, malware, and ransomware.
“By infecting files and programs on computers, the virus moves across the internet. Among other things, malware is designed to harm computer systems, networks, and servers. The program named ransomware encrypts user files and asks for money inorder to give out decryption keys.”
3. How can a firewall protect a network?
A network firewall safeguard data traffic entering and leaving a system according to specified security rules. It acts as a barrier between safe and unsafe sections of a network. Without it, the way a network operates would change and its security lessened compared to if there were no wall at all. Its main task is monitoring ongoing activities to prevent malicious entities from accessing the system. There are threats lurking around which make a firewall necessary as it protects against them.
4. What cybersecurity skills are in demand?
The cybersecurity expertise that is wanted follows:
i) Network security
ii) Risk management
iii) Threat analysis and intelligence
iv) Incident response
v) Security operations
vi) Penetration testing
vii) Cryptography
viii) Cloud security
ix) Compliance and regulatory knowledge
5 . How does a firewall improve network security?
A firewall performs security functions by blocking outsiders from gaining unauthorized entry, separating undesirable data packets, and examining activities in the network to identify and prevent harmful operations.
6. What is the meaning of a secure password, and what are its examples?
To figure out and crack good password you will need plenty of work to put. The password should be unique and strong. A combination of uppercase and lowercase letters, along with numbers and special characters is required for your safety. By the way, “P@ssw0rd#07” is a safe password.
7. What are the common techniques for securing a computer network?
To shield your network, you can: erect firewalls, pay attention to the software which has not had updates made on it, deal with all sorts of security vulnerabilities, be aware of threats, carry out security checks, switch on attack detection/prevention technologies, as well as use tough passwords alongside other forms of login including two-factor and multi-factor authentication.
8. What is two-factor authentication, and why is it important?
Two-factor authentication or 2FA is a security feature that necessitates more than one way to prove a person’s identity before granting access to its system or data. This could be a combination of something you know (password) and something you own (phone).
9. What exactly are encryption and decryption?
Encrypting is the process of transforming ordinary language into cyphertext, which obfuscates the original text, hence making it difficult to be read. Decrypting is the act of altering cyphertext back into natural language so that it can be understood once more by human beings.
10. What is security auditing?
In cybersecurity, a security audit examines the whole of a firm’s computer systems, its policies, and their functions, with a view to identifying areas of vulnerability that can be exploited by unauthorized users.
11. What steps would you take if you discovered a security breach?
When a security breach occurs, follow these guidelines:
i) Isolate infected systems.
ii) Prevent further spread of the breach.
iii) Notify relevant individuals and authorities.
iv) Investigate the incident.
v) Remove the cause of breach.
vi) Rebuild and restore contaminated systems and information.
vii) Employ measures to avoid future breaches.
12. What is social engineering? Give an example.
Tricking people into giving away personal sensitive information is what it’s all about. For example, one could impersonate the CEO and call or email a staff member to request that they provide information regarding company portal passwords
13. What are cookies in a web browser?
Cookies are information stored in your device by the web browser to help you browse the Web better, entering your preferences, login data, and tracing websites you visited.
14. Define what a security policy is.
A security policy is a document that tells everyone in the organization what the security should be.
15. How can you prevent a Man-In-The-Middle attack?
To prevent MitM Attacks, thee simple measures can be taken:
i) Encrypting the communication using proper encryption
ii) Voice communication through secured channels
iii) Verification of authenticity of digital signature
iv) Implementing 2FA before login
v) Deploying VPNs
vi) Keeping systems updated and well patched.
16. What is a honeypot in cybersecurity?
A honeypot is like a fake system or network set up by people to deceive someone hacking. It observes, tracks and studies assaults to ensure improved security.
17. What is the concept of digital signature?
If you get an email, you probably don’t worry about whether it is really from the person it says it’s from.
18.What are the common cyber threats today?
These days, there are several cyber threats which include;
i) Phishing attack
ii) Malware
iii) Denial of Service attack
iv) Insider threat
v) Zero-day exploit
vi) Man-in-the-middle attack
vii) Social engineering attack
19. What is the role of patch management in maintaining security?
Patching maintains the timeliness of software and systems. It is the act of addressing malfunctions and such issues in order to avert criminal abuse of previously known flaws.
Part D – Cybersecurity Interview Questions for Intermediates
1 . What are the different types of network security?
Below are different types of network security for various aspects that might make communication easier.
i) Firewall-Security: – This type of security tends to watch and also do digestion of network traffic as it either gets into or even goes out of a certain network.
ii) Intrusion Detection System (IDS):– It checks network traffic to identify any form of suspicious activity that may eventually breach the pre-defined strategies implemented by an organization. Intrusion prevention systems are basically systems put in place to put away from the network of those activities that are suspicious
iii) Virtual Private Networks (VPNs) are able to provide protection for unsafe connections over the internet.
iv) Antivirus and Anti-Malware Software-This Software helps to prevent from malware and viruses.
v) Who has the right to make use of resources on the network are managed through access controls.
vi) While data is moving around, it is kept secure using encryption. vii) To limit attacks, a network is divided into smaller components in network segmentation.
viii) Security Information Management together with Security Event Management (SIEM) – this audits and analyzes logs from different types of network devices with the aim of identifying and responding to security incidents in real-time.
2 . What are the concepts of PKI?
Public Key Infrastructure deals with digital keys and certificates. It is made up of a certification body (CA), the registration authority (RA), digital certificates, public and private keys, cancellation list of certificates (CRL), and a model of trust.
3. What are the key elements of a strong security policy?
“An effective security policy comprises the following features: access control encryption, regular updates, incident response, compliance, training and awareness.”
4. How does a rootkit work, and how would you detect it?
rootkit is a type of malicious software that enables hackers to gain unauthorized access to one’s system. It attempts to conceal itself and can assume root or admin privileges on computers it infects to tamper with files contained within them.”
5. What is a zero-day vulnerability?
They are zero-day vulnerabilities. That means the software has bugs which the company hasn’t discovered. So there’s no patch available right now. At present there’s no fix either. Consequently, hackers have an opportunity to cause harm rapidly.
6. Explain the ISO 27001/27002 standards.
Let’s discuss the ISO 27001/27002 standards. ISO 27001: Addresses how to build , use, sustain , and enhance an Information Security Management System (ISMS). ISO 27002: Provides guidance on the approach companies can adopt to establish their own rules that ensure data is not compromised.
7. How do threat detection systems work?
These systems monitor the activities on the network, including the system logs, and use the rules and smart computer programs to discover their potential threats and abnormal behavior.
8. What is the principle of ethical hacking?
At a point when he or she is given permission to enter systems and locate and correct security weaknesses. The rule it conforms to is the “Do no harm rule. They notify people of the results of their discoveries and assist them in repairing them without causing any damage to any property.”
9. What are the concepts of risk assessment?
Risk assessment is the act of identifying and evaluating risks within information systems by recognizing dangers, examining vulnerabilities, and taking action against them.
10. What are three ways to safeguard against cyber-attacks?
There are many ways to prevent cyber-attacks, including:
i) Regular software updates are essential to keep this kind of problem under control because they keep the system and applications in use up-to-date.
ii) Employee training and awareness is another method that can be used to prevent these attacks; it involves more just telling workers what these dangers might look like but also teaching them about good online safety practices.
iii) Secondly, using multi-factor authentication would make user accounts more secure.
11. What is incident response, and how is it managed?
In dealing with cyber-attacks, companies have to respond to incidents, which entail identifying the problem, addressing it and learning from it; this is done by following a clear series of steps as laid down in a laid down plan.
12. What is the principle of least privilege?
The concept of least privilege goes along the lines of granting employees adequate rights to help them carry out their duties.
13. How does Secure Socket Layer (SSL) work?
SSL lets you keep your data private. What this means is that whatever happens between your browser and a website hackers will not be able to access it because the information is scrambled.
14.What is network sniffing?
This refers to a scenario where malevolent people intercept data exchanged over the Internet connection. This enables them to capture user credentials for misuse during online transactions or accessing other confidential account details like bank records.
15.Why is a disaster recovery plan important?
In case of any major issue, like a cyber attack or a natural disaster, a company can refer to the disaster recovery plan.
16.What is a Security Information and Event Management (SIEM) System?
A system for gathering and analyzing data on security threats in order to identify and counter them takes information from various sources. All security activity is monitored.
17. How do you manage cryptographic keys?
Assuming that you want to access, you need to create, save and use your cryptographic keys. One must maintain his keys secretively, frequently change them and protect them with tough passwords.
18. What are the common methods for secure data disposal?
It is possible to destroy, paper files by cutting them up, clean hard drives with programs and cause damage to storage devices as an example of what is in this unwanted data.
19. What are the three main steps of endpoint security?
Endpoint security has three major components which are:
i) It is all safeguarding devices using antivirus as well as firewalls.
ii) It keeps updating software continuously through fixes
iii) It involves monitoring devices for any suspicious activities occurring.
20. What is the role of artificial intelligence in cybersecurity?
AI helps to identify and address cyber threats in a relatively simple way. Further, it is effective in analyzing significant volumes of data within a short period, hence identifying encryptions that human specialists cannot detect.
21.What are the challenges in cloud security?
“The field of cloud security has been fraught with challenges such as data protection against malicious individuals,hence ensuring only authorized individuals have access to it. Similarly, privacy becomes a major concern with shared cloud infrastructure.”
22.What is a Security Operations Center (SOC)?
A Security Operations Center, which consists of a group of individuals, is responsible for monitoring any security issues that may occur, as well as responding accordingly.
23.Why is cybersecurity compliance important?
Why is it important for companies to follow cybersecurity rules? Because following cybersecurity rules means that a company is observing the law. This aids it in protecting data, avoiding penalties as well as enhancing trust among clients.
24.What Is multi-factor authentication, and how does it enhance security?
You have to present yourself as who you are by at least two different methods before accessing your account using multifactor authentication which boosts security by increasing the difficulty level for hackers who might have accessed only your password.
Part E – Cybersecurity Interview Questions for Experienced
1. What are the challenges for secure IoT?
Here is list of things that make security of IoT devices difficult:
i) Lack of proper protection measures: Numerous internet-of-things gadgets compromise user security.
ii) Several attacking options: More devices mean more potential entry points for hackers.
iii) Disorganized infrastructures: With numerous different types of objects as well as arrangements, ensuring total security becomes impossible.
iv) Ensuring privacy: It is never easy to prevent unauthorized access to personal information.
v) Not enough power: These devices lack much processing power or memory, so it’s difficult to add strong security.
2. What is an advanced persistent threat?
Advanced persistent threat is related to someone who breaks into a network and remains undetected for a long time hoping to access information or spy on activities.
3. Explain the role of blockchain in cybersecurity.
In order to enhance online transactions and minimize their vulnerability to fraud, blockchain has been introduced for the very same reason. Henceforth, a shared transaction record store is created by these blocks or units against tempering with them. The records are so kept to maintain integrity within themselves regarding all the activities that have taken place in this chain or series of chronological data. Additionally, correctness of information is checked while dishonesty is controlled hence making this platform open and transparent.
4. How do you approach securing a large, distributed network?
Approaches to keep our network safe
i) Divide the network: Break it down into smaller sections manageable.
ii) Employ firewalls and intrusion detection systems (IDS): Make sure each section is monitored and guarded.
iii) Multiple factor authentication (MFA) and strong passwords should be used to guarantee the real identity of a person
iv) Always update: Patch vulnerabilities in any system
v) Always stay aware of current affairs”.
5. What is the importance of forensics in cybersecurity?
When it comes to understanding the specifics of a cyber attack and their respective origins, forensics is of utmost significance. This data can prevent future intrusions as well as act as evidence during court cases.
6. Explain the intricacies of network protocol security.
Here is what network protocol security encompasses:
i) Use encryption to protect data when it moves.
ii) Verify user identities and device authenticity.
iii) Confirm that transmitted data has not been tampered with.
iv) Restrict who can access what on a network.
7. How do you manage security in a DevOps environment?
i) Insert security validation points into the DevOps process: Deploy tools aiming at automating security validation without human intervention.
ii) Monitor continuously: Observe every activity of software development and distribution.
iii) Educate on security: Explain to developers how one can write secured code.
iv) Collaborate: Ensure that teams responsible for security, development, and operations have discussions among themselves.
8. What is the concept of micro-segmentation?
A network is divided into minute fractions at the very small scale while this makes it difficult for hackers to manoeuvre throughthe network in case they infiltrate a small part.
9. What are the challenges in securing big data?
The following are problematic areas related to securing big data:
i) Volume: Managing and safeguarding huge volumes of information is a cumbersome task.
ii) Variety: Several methods are required to guarantee the safety of different kinds of data.
iii) Velocity: There is a need for real-time security solutions for data moving at very high speeds.
iv) Complexity: It might be difficult to apply security controls for large data environments.
10.What are your strategies for managing supply chain risks in cybersecurity?
Here is how to manage supply chain risks in cybersecurity:
i) Should check out and inspect how secure they were regularly
ii) Stipulate safety regulations in agreements
iii) Monitor supplier’s activities and their safety measures all the time
iv) If they occur, have contingencies against supply chain issues.
11.What is container security?
As far as container security goes, it’s all about making sure that your containerized applications as well as the environment housing them are protected from any harm. This involves employing certain tactics such as running scans over your images, making sure they are not infected by computer viruses or malware, and segmenting networks.
12.How do you ensure compliance with international data protection laws (like GDPR)?
To remain informed about the international regulations on data safety, the following steps should be taken.
1. Evaluate your data processes: Analyze how you manage data at least every week.
2. Introduce regulations: Create rules that coincide with the legal requirements.
3. Educate your staff: Ensure your workers understand their responsibilities.
4. Document everything: Record how data is utilized properly.
5. Continue monitoring: Carry out regular assessments to determine compliance with the regulations.”
13. Explain the future trends in cybersecurity.
i) Intangible burglar alarm systems and automated brainpower: All of this will enable a person to identify potential problems, and work them out.
ii) Principle of no trust: forever check, do not just believe.
iii) Quantum cryptography will protect data from quantum-attacking machines.
iv) Security of the Internet of Things will give better experience in defending interconnected devices.
v) Cloud safety includes methods to protect data, which is kept there in various forms.
14. What are the ethical considerations in cybersecurity?
i) Respecting and safeguarding individual details is vital.
ii) Confidentiality:It is essential to be honest about security procedures in addition to breaches incase.
iii) Integrity: At what time things go wrong, someone ought to acknowledge accountability for the security steps.
iv) Equality: A uniform maximum defense ought to be given to everyone.
15. How do you measure the effectiveness of a cybersecurity program?
Track numbers: Keep an eye on issues at work, speed of addressing them and adherence to rules. Check often: browse over the security setting within and outside the organization Test attacks: Attempt a penetration test. Find and correct vulnerabilities Ask users: Request feedback from users utilizing the security tools.
16. What are the challenges of wireless networks?
Wireless networks are hard to set up for a number of reasons:
i) Signals could be disrupted by walls or other devices
ii) sometimes the signal has to be made strong everywhere it is needed n
iii) To prevent unauthorized access and data theft, we sometimes have to control the amount of stuff traveling around and maintain the network’s health.
17. What is quantum cryptography, and what are its implications for security?
Quantum cryptography applies quantum mechanical concepts to create highly secure communication methods. Accordingly, this would make it quite challenging to decrypt such encryption, hence necessitating fresh methods of keeping our privacy undisturbed since quantum computers could lead to disarray.
18. What is the concept of federated identity management?
Federated identity management can be achieved by enabling users to employ a single sign-in for multiple systems. Such an arrangement is meant to simplify such tasks besides enhancing security as the user does not have to grapple with multiple passwords and all the checks are done in one place.
19. What are the latest developments in cybersecurity threats?
Cyber security is in a fix: Ransomware is evolving to become more sophisticated as hackers practice selectiveness and brilliance while choosing their targets; hacking into software updates or even other services among victims’ organizations is widespread; however -60% remain unprotected due its complexity-; since now malevolent agents have resorted to using AI to make their bogus mails seem more logical as well as vicious codes efficient; no one knew about the faults that could be exploited up to this day.
20. How do you manage security in a hybrid cloud environment?
The way to defend a hybrid cloud setup is as follows:
Utilize the same security procedures in the cloud as within your organization. This means that every computer must have strong passwords (greater than 8 characters) along with automatic logout after some time if there is no user activity going on (say about 30 minutes maximum).
Safeguarding our vital information throughout its entire lifecycle involves securing it while at rest or in transit(locking doors but leaving windows open). Whether data is sitting idle or on the move, it should be shielded from unauthorized access using encryption mechanisms like SSL/TLS during communication between points of presence.
To make sure that only legitimate persons can access anything, use stringent authorization checks all over everything i.e. your files, your software projects,etc., by checking if they are who they claim to be. This involves developing stringent access-control policies that compel each user to authenticate themselves before gaining access to specific systems/resources.
21. How does AI affect cyber threats?
“Cybersecurity can be made better or worse by AI. Although it assists in the quicker detection and repulsion of attacks, it is also exploited by attackers who use it to create more sophisticated and sinister threats.”
22. What is the role of machine learning in detecting cyber threats?
Machine learning detects unusual occurrences and potential threats by analyzing patterns and behavior of things. In this way, it improves accuracy and expediency of threat detection.
23. What is the application of threat intelligence?
Threat intelligence is all about collection and analysis of data that pertains to new threats in place thereby helping in the anticipation, deterrence and response to future cyber-attacks.
24. What strategies would you implement for securing mobile applications?
In order that mobile apps become safer, one should:
i) Write code that would not crack under common vulnerabilities.
ii) Correct security issues through updates.
iii) Log users in using strong methods.
iv) Encrypt the information stored in the program and sent through it.
25.Explain the challenges and solutions in endpoint detection and response (EDR)
Issues Various devices: It is difficult to secure all sorts of gadgets Excess information: There is a lot of data to look through from endpoints Cunning attackers: Some attacks are really sneaky and very hard to notice Solutions Innovative tools: EDR things can see and respond to issues immediately Studying suspicious behavior: We combine EDR with other security solutions to enhance overall safety Collaboration: We integrate EDR along with other security tools for better protection.
I hope these Cybersecurity Interview Questions will help you perform well in your interview. To become expert join our Cyber Security Masters Program today. And I wish you all the best!
If you wish to learn more and build a colorful career, then check out our Cyber Security Course in India which comes with instructor-led live training and real-life project experience. This training will help you understand Linux Administration in-depth and help you achieve mastery over the subject.
You can also take a look at our newly launched course on CompTIA Security+ Certification which is a first-of-a-kind official partnership between Edureka & CompTIA Security+. It offers you a chance to earn a global certification that focuses on core cybersecurity skills which are indispensable for security and network administrators.
Also, learn Cybersecurity the right way with Edureka’s POST GRADUATE PROGRAM with NIT Rourkela and defend the world’s biggest companies from phishers, hackers and cyber attacks.
Got a question for us? Please post it on Edureka Community and we will get back to you.
