Data is the most valuable asset, which is the reason why data security has become an international agenda. Data breaches and security failures can put the world economy at risk. Realizing the need for national and economic security, the President of US issued an Executive Order to develop a Cybersecurity Framework to help reduce cyber risks. Dive deeper into the feed to know more about the Frame.
Why Cybersecurity Framework?
Implementing the Framework is effective because:
- It Results in a shift from compliance to action and specific outcomes
- It has built-in maturity model and gap analysis so you don’t need additional maturity model on top of CSF
- It gives you a measure of where you are and where you need to go
- It can be implemented in stages or degrees which makes it more appealing to business
What is Cyber Security?
his Edureka video on “What is Cyber Security” gives an introduction to the Cyber Security world and talks about its basic concepts.
What is Cybersecurity Framework?
Developed through coordinated effort amongst business and government, the intentional Framework comprises of measures, rules, and practices to showcase the safety of imperative foundation. The organized, adaptable, repeatable, and effective approach of the Framework helps house proprietors and administrators of critical foundation to oversee cybersecurity-related hazard.
Objectives of Cybersecurity Framework
Check out our new CEH (v13) – Certified Ethical Hacker course to learn the in-depth concepts of ethical hacking and get skilled.
Types of Cybersecurity Framework
The most frequently adopted frameworks are:
- PCI DSS (Payment Card Industry Data Security Standard): It is a set of security controls required to implement to protect payment account security. It is designed to protect credit card, debit card, and cash card transactions
- ISO 27001/27002 (International Organization for Standardization ): Best practice recommendations for information security management and information security program elements.
- CIS Critical Security Controls: A prescribed arrangement of activities for cyber protection that give particular and noteworthy approaches to stop the present most inescapable and perilous attacks. A key advantage of the Controls is that they organize and center fewer activities with high outcomes
- NIST Framework: A Framework for improving critical infrastructure Cybersecurity with a goal to improve organization’s readiness for managing cybersecurity risk by leveraging standard methodologies and processes
Ready to take your career in cybersecurity to the next level? CISSP Certification is the way!
Components of Cybersecurity Framework
There are three key components: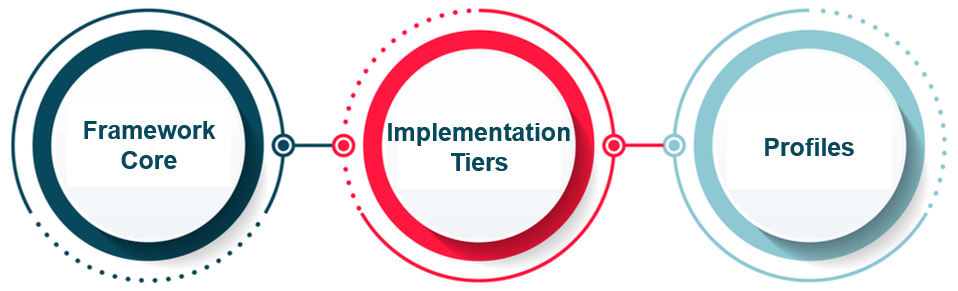
Framework Core: It gives an arrangement of required Cybersecurity exercises and results utilizing normal understandable language. The Core guides associations in overseeing and decreasing their Cybersecurity chances in a way that supplements an association’s current Cybersecurity and risk management processes.
Implementation tiers: It helps associations by giving setting on how an association sees Cybersecurity risk management. The tiers manage associations to consider the suitable level of thoroughness for their cybersecurity program and are regularly utilized as a specialized device to talk about hazard hunger, mission need, and spending plan.
Profiles: Profiles are an association’s novel arrangement of their organizational prerequisites and goals, and assets against the coveted results of the Framework Core. Profiles are principally used to recognize and organize open doors for enhancing Cybersecurity at an association.
Cybersecurity Framework’s Five Functions
The Functions are the largest amount of deliberation incorporated into the Framework. They go about as the foundation of the Framework Core that every single other component is sorted out around. The five functions included in the framework are: 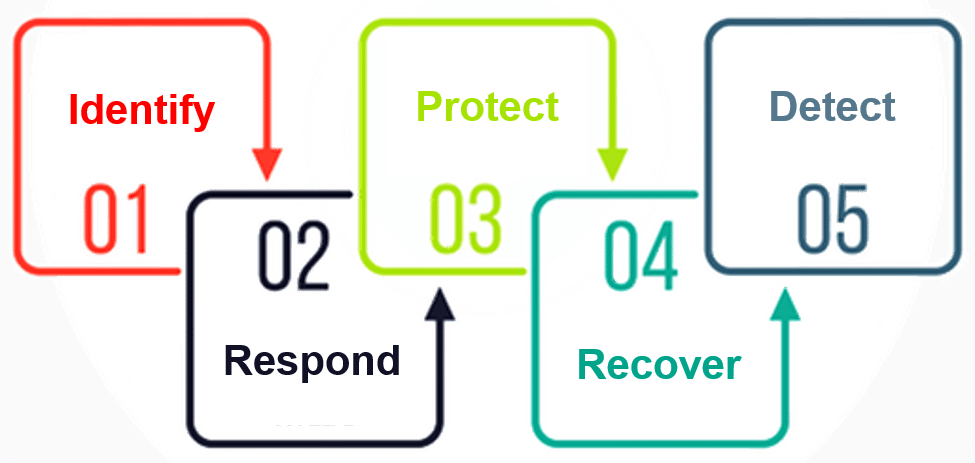
- Identify: The Identify Function helps with building up a hierarchical comprehension in overseeing cybersecurity to frameworks, individuals, resources, information, and capacities.
- Protect: The Protect Function diagrams proper shields to guarantee conveyance of basic foundation administrations. The Protect Function underpins the capacity to restrict or contain the effect of a potential Cybersecurity occasion.
- Detect: The Detect Function characterizes the fitting exercises to recognize the event of a Cybersecurity occasion. The Detect Function empowers opportune revelation of Cybersecurity occasions.
- Respond: The Respond Function incorporates proper activities to make a move in regards to a distinguished Cybersecurity occurrence. The Respond Function bolsters the capacity to contain the effect of a potential Cybersecurity occurrence.
- Recover: The Recover Function distinguishes proper exercises to keep up plans for versatility and to reestablish any abilities or administrations that were impeded because of a Cybersecurity event.
Enroll in a prestigious Cyber Security Internship program to kickstart your career.
Requirement Categories of each function
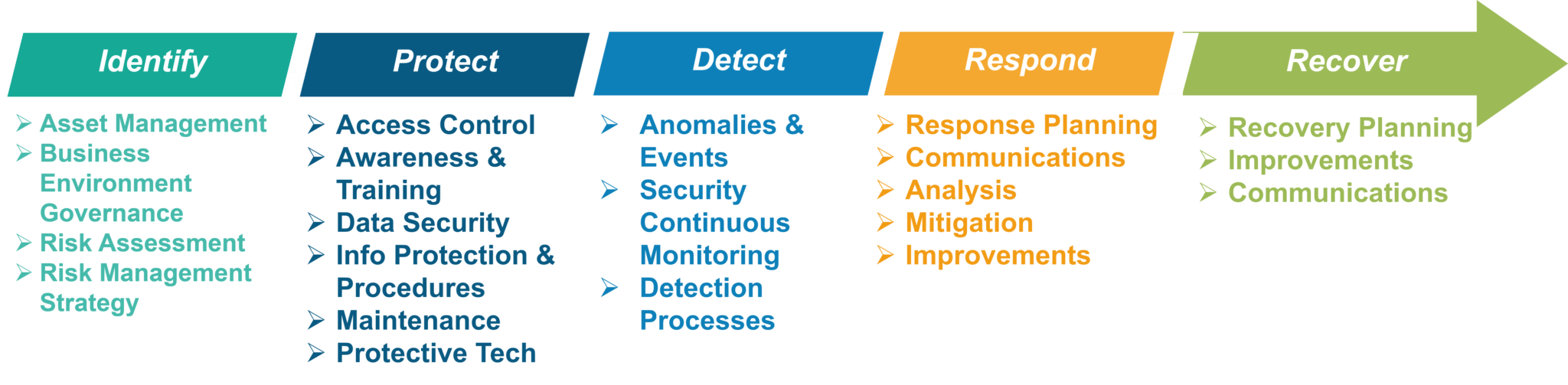
Alright, having discussed the functions and components of the framework, let’s see how these frameworks are used.
Using Cybersecurity Framework
Using the framework could improve the critical infrastructure of an organization. The Framework can be implemented in stages and hence can be tailored to meet any organization’s needs. The Framework is intended to supplement, not replace, an association’s cybersecurity program and risk administration forms. 
Who Should Use the Framework?
The Cybersecurity Framework is for associations of all sizes, divisions, and developments. The framework was designed to be extremely adaptable. With built-in customization option available the framework can be modified to be used by any organizations.
A small association with a low cybersecurity spending plan, or an extensive enterprise with a major spending plan, are each ready to approach the result in a way that is attainable for them. It is this adaptability that enables the Framework to be utilized by associations which are simply beginning in setting up a cybersecurity program, while additionally offering some incentive to associations with develop programs.
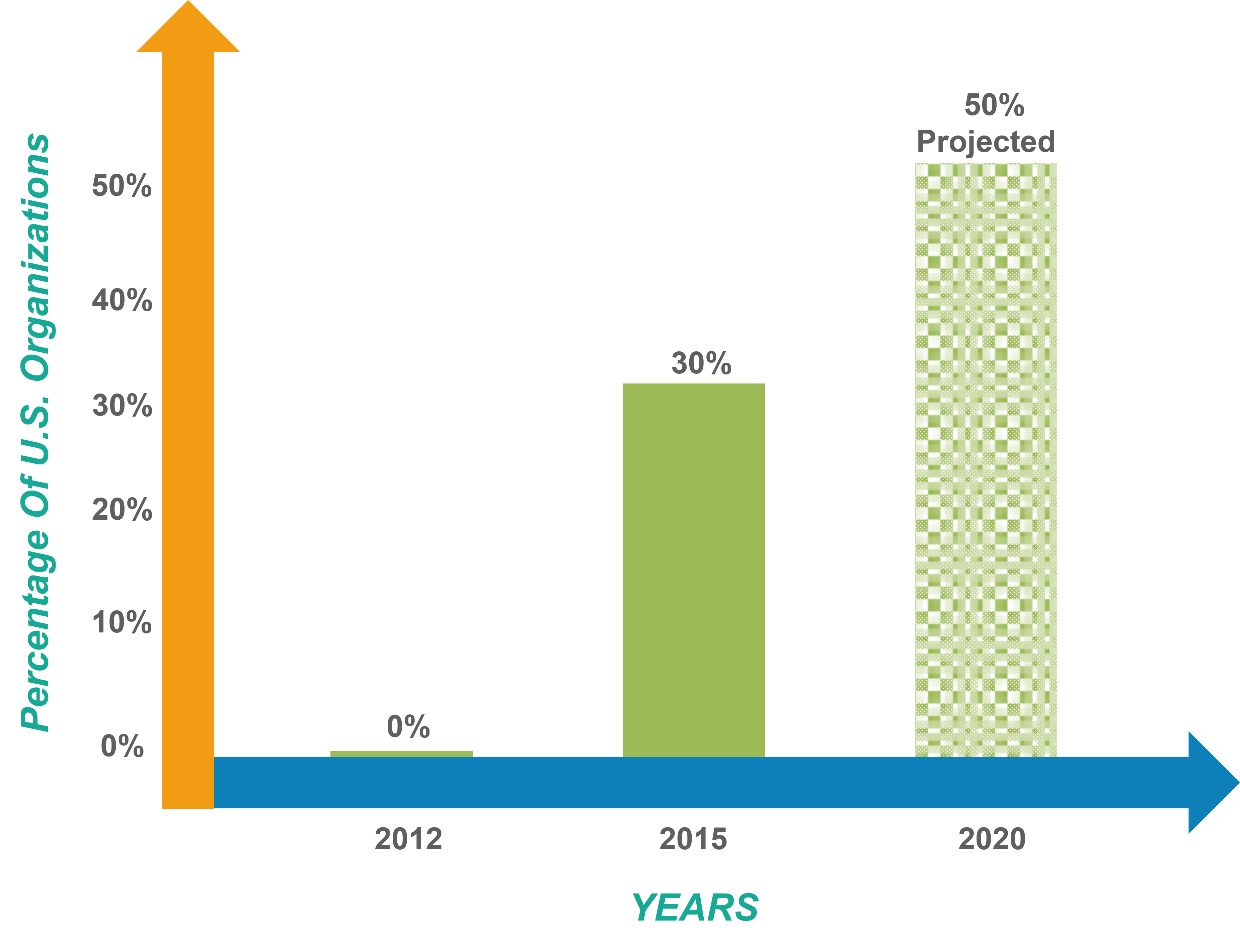
How Are Organizations Using the Framework?
In the course of recent years, NIST has been watching how the network has been utilizing the Framework. These are some regular examples that we have seen develop:
- Authority has grabbed the vocabulary of the Framework and can have educated discussions about cybersecurity chance
- Associations have utilized the levels to decide ideal levels of hazard administration
- Associations are finding the way toward making profiles to a great degree powerful in understanding the present cybersecurity hones in their business condition
- Profiles and execution designs are being utilized in organizing and planning for cybersecurity change exercises
Steps to Implement Cybersecurity Framework
The Cybersecurity Framework defines 7 steps for establishing a cybersecurity program: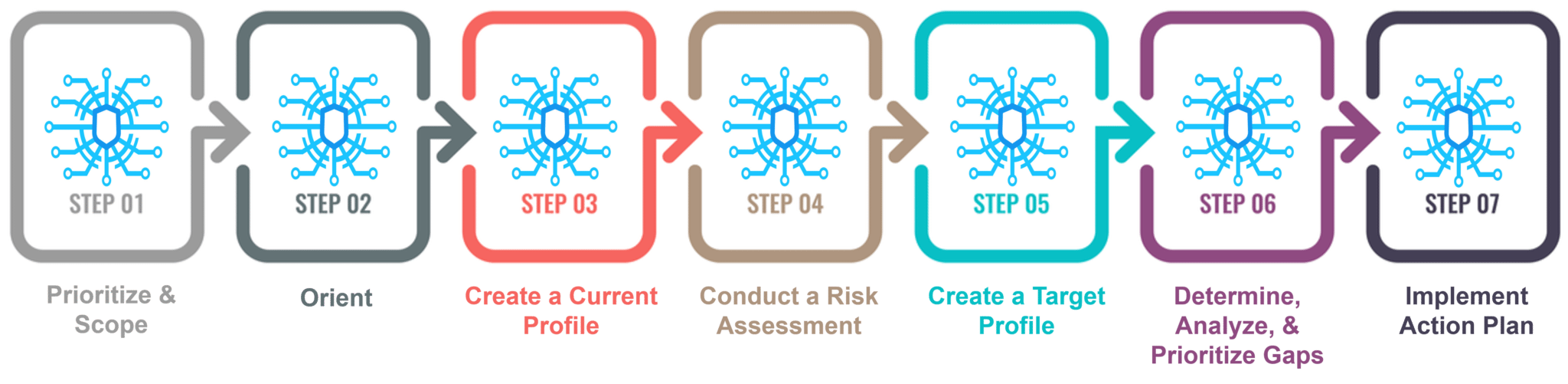 Example of Organization’s Using the Cybersecurity Framework
Example of Organization’s Using the Cybersecurity Framework
Nuclear Sector Cybersecurity Framework Implementation:
Atomic reactors in the United States have a solid reputation of cooperating to create and execute digital security principles, devices, and procedures that guarantee wellbeing, security, and unwavering quality.
Framework Implementation Benefits:
The Framework is intended to be sufficiently adaptable to be utilized both by associations with developing digital security and risk administration programs and by those with less-created programs.
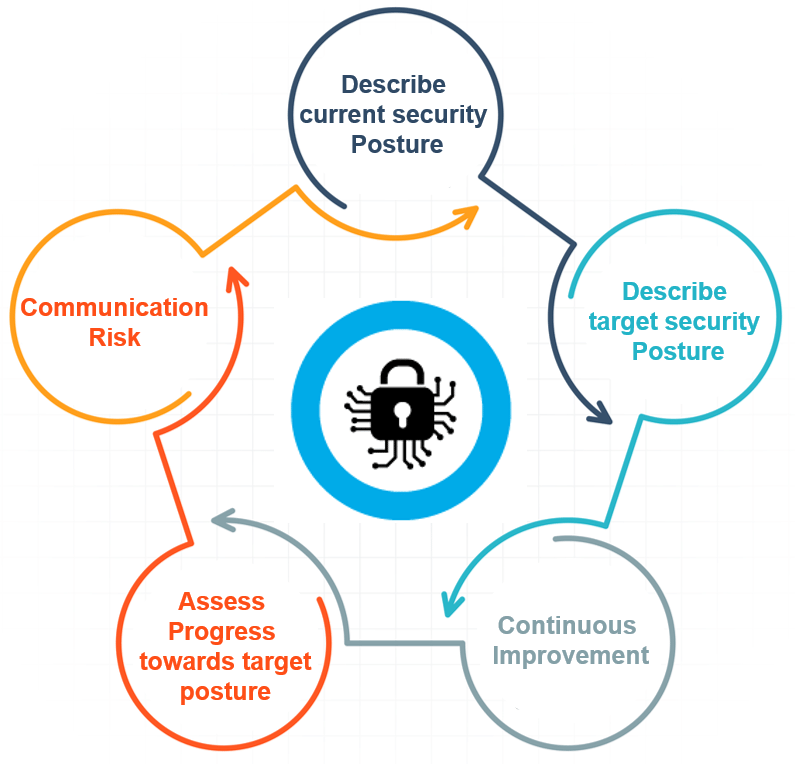
As a rule, implementing the Framework gives an instrument to associations to:
- Evaluate and particularly depict its current and focused on digital security pose
- Identify gaps in its present projects, procedures, and workforce
- Identify and organize open doors for development utilizing a persistent and repeatable process
- Assess advance toward achieving its objective digital security act
- Demonstrate the association’s arrangement with the Framework’s broadly perceived accepted procedures
- Highlight any present practices that may outperform the Framework’s prescribed practices
- Communicate its digital security act in a typical, perceived dialect to inside and outside partners—including clients, controllers, financial specialists, and approach producers
Here’s how the Cybersecurity Framework was used to demonstrate how cybersecurity practices at U.S. nuclear power plants align to the Framework.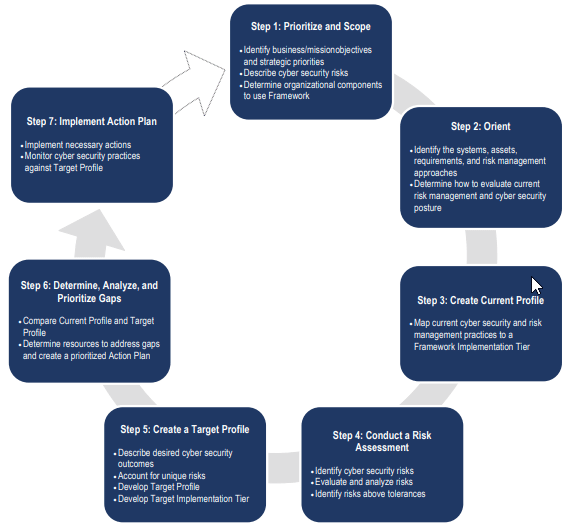
I hope this blog was helpful and now you have a basic understanding of Cybersecurity Frameworks. Stay tuned for more blogs by Edureka.
If you wish to learn Cybersecurity and build a colorful career in cybersecurity, then check out our Cyber Security Certification Training which comes with instructor-led live training and real-life project experience or join our Masters in Cyber Security. This training will help you understand Cybersecurity in depth and help you achieve mastery over the subject.
You can also take a look at our newly launched course on CompTIA Security+ Training Course which is a first-of-a-kind official partnership between Edureka & CompTIA Security+. It offers you a chance to earn a global certification that focuses on core cybersecurity skills which are indispensable for security and network administrators.
Got a question for us? Please mention it in the comments section and we will get back to you or join our Cyber Security training in Salem.


















great video!!!!!