Adoption of Internet by businesses and enterprises has made mobile-banking, online shopping, and social networking possible. Whilst it has opened up a lot of opportunities for us, its not altogether a safe place because its anonymity also harbors cybercriminals. So, to protect yourself against the cyber threats of today, you must have a solid understanding of cybersecurity. This article will help you get a grip on cybersecurity fundamentals.
The History of Cybersecurity
About forty years ago words like worms, viruses, trojan-horse, spyware, malware weren’t even a part of conventional information technology (IT) vocabulary. Cybersecurity only came into existence because of the development of viruses. But how did we get here?
The history of cybersecurity began as a research project. In the 1970’s, Robert Thomas, a researcher for BBN Technologies in Cambridge, Massachusetts, created the first computer “worm”. It was called The Creeper. The Creeper, infected computers by hopping from system to system with the message “I’M THE CREEPER: CATCH ME IF YOU CAN.” Ray Tomlinson, the inventor of email, created a replicating program called The Reaper, the first antivirus software, which would chase Creeper and delete it.
Late in 1988, a man named Robert Morris had an idea: he wanted to test the size of the internet. To do this, he wrote a program that went through networks, invaded Unix terminals, and copied itself. The Morris worm was so aggressive that it slowed down computers to the point of being unusable. He subsequently became the first person to be convicted under Computer Fraud and Abuse Act.
From that point forward, viruses became deadlier, more invasive, and harder to control. With it came the advent of cybersecurity.
Join the elite cybersecurity professionals and boost your career with CISSP Certification Training Online
Cyber Security Full Course In 8 Hours
This Edureka video on “Cyber Security Full Course” will help you understand and learn the fundamentals of Cyber Security. This Cyber Security Tutorial is ideal for both beginners as well as professionals who want to master the Cyber Security concepts.
What is cybersecurity?
Cybersecurity is the body of technologies, processes, and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access.
The term cybersecurity refers to techniques and practices designed to protect digital data. The data that is stored, transmitted or used on an information system. After all, that is what criminal wants, data. The network, servers, computers are just mechanisms to get to the data. Effective cybersecurity reduces the risk of cyber-attacks and protects organizations and individuals from the unauthorized exploitation of systems, networks, and technologies.
Robust cybersecurity implementation is roughly based around three key terms: people, processes, and technology. This three-pronged approach helps organizations defend themselves from both highly organized attacks and common internal threats, such as accidental breaches and human error.
The attacks evolve every day as attackers become more inventive, it is critical to properly define cybersecurity and understand cybersecurity fundamentals.
Read related post Cybersecurity vs information security
Why is cybersecurity important?
Listed below are the reasons why cybersecurity is so important in what’s become a predominant digital world:
- With each passing year, the sheer volume of threats is increasing rapidly. According to the report by McAfee, cybercrime now stands at over $400 billion, while it was $250 billion two years ago.
- Cyber attacks can be extremely expensive for businesses to endure. In addition to financial damage suffered by the business, a data breach can also inflict untold reputational damage.
- Cyber-attacks these days are becoming progressively destructive. Cybercriminals are using more sophisticated ways to initiate cyber attacks.
- Regulations such as GDPR are forcing organizations into taking better care of the personal data they hold.
Because of the above reasons, cybersecurity has become an important part of the business and the focus now is on developing appropriate response plans that minimize the damage in the event of a cyber attack. But, an organization or an individual can develop a proper response plan only when he has a good grip on cybersecurity fundamentals. Enroll with our masters in cyber security program to become the expert.
Now that we know what cybersecurity is and why it is important. Check out our new CEH (v13) – Certified Ethical Hacker course to learn the in-depth concepts of ethical hacking and get skilled. Let’s take a look at fundamental objectives of cybersecurity.
The CIA Triad
Confidentiality, integrity, and availability, also known as the CIA triad, is a model designed to guide companies and organizations to form their security policies. Technically, cybersecurity means protecting information from unauthorized access, unauthorized modification, and unauthorized deletion in order to provide confidentiality, integrity, and availability.
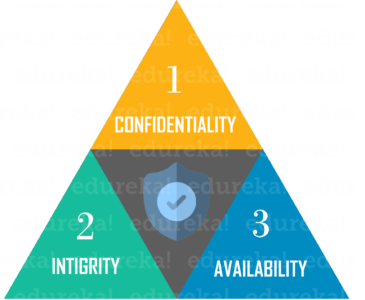
Let’s explore these components and some of the information security measures which are designed to assure the safety of each component.
Also Read: CISSP Certification Requirements – Complete Guide
Cybersecurity Fundamentals – Confidentiality
Confidentiality is about preventing the disclosure of data to unauthorized parties. It also means trying to keep the identity of authorized parties involved in sharing and holding data private and anonymous. Often confidentiality is compromised by cracking poorly encrypted data, Man-in-the-middle(MITM) attacks, disclosing sensitive data.
Standard measures to establish confidentiality include:
- Data encryption
- Two-factor authentication
- Biometric verification
- Security tokens
Enroll in a prestigious Cyber Security Internship program to kickstart your career.
Integrity
Integrity refers to protecting information from being modified by unauthorized parties. It is a requirement that information and programs are changed only in a specified and authorized manner. Challenges that could endanger integrity include turning a machine into a “zombie computer”, embedding malware into web pages.
Standard measures to guarantee integrity include:
- Cryptographic checksums
- Using file permissions
- Uninterrupted power supplies
- Data backups
Availability
Availability is making sure that authorized parties are able to access the information when needed. Data only has value if the right people can access it at the right time. Information unavailability can occur due to security incidents such as DDoS attacks, hardware failures, programming errors, human errors.
Standard measures to guarantee availability include:
- Backing up data to external drives
- Implementing firewalls
- Having backup power supplies
- Data redundancy
All cyber attacks have the potential to threaten one or more of the three parts of the CIA triad. Confidentiality, integrity, and availability all have to work together to keep your information secure. So, It’s important to understand what the CIA Triad is, how it is used to plan and implement a quality security policy while understanding the various principles behind it.
How much does cybersecurity jobs pay?
With the widely reported success of massive global cyber-attacks, like WannaCry and Adylkuzz, companies are paying more than ever to land highly qualified cybersecurity professionals to secure their most vulnerable assets. The average salary range for top cybersecurity job roles falls between $100,000 to $210,000.
This brings us to the end of this article ond Cyber security Fundamentals. I hope you all had something new to learn.
If you wish to learn cybersecurity framework and build a colorful career in cybersecurity, then check out our Cyber Security Certification course which comes with instructor-led live training and real-life project experience. You can also take a look at our newly launched CompTIA Security Plus Certification Training which is a first-of-a-kind official partnership between Edureka & CompTIA Security+. It offers you a chance to earn a global certification that focuses on core cybersecurity skills which are indispensable for security and network administrators.
Got a question for us? Please mention it in the comments section of “Cybersecurity Fundamentals” and we will get back to you or join our Cyber Security Training in Boston today.



















