Encryption is essentially important because it secures data and information from unauthorized access and thus maintains the confidentiality. Here’s a blog post to help you understand ” what is cryptography “ and how can it be used to protect corporate secrets, secure classified information, and personal information to guard against things like identity theft.
You can go through this ‘What is Cryptography’ video where our Cyber Security Training expert is discussing each & every nitty-gritty of the technology.
What is Cryptography
Cryptography is essential to protect the information shared across the internet. This video on What is cryptography explaines you the fundamental concepts along with various encryption techniques.
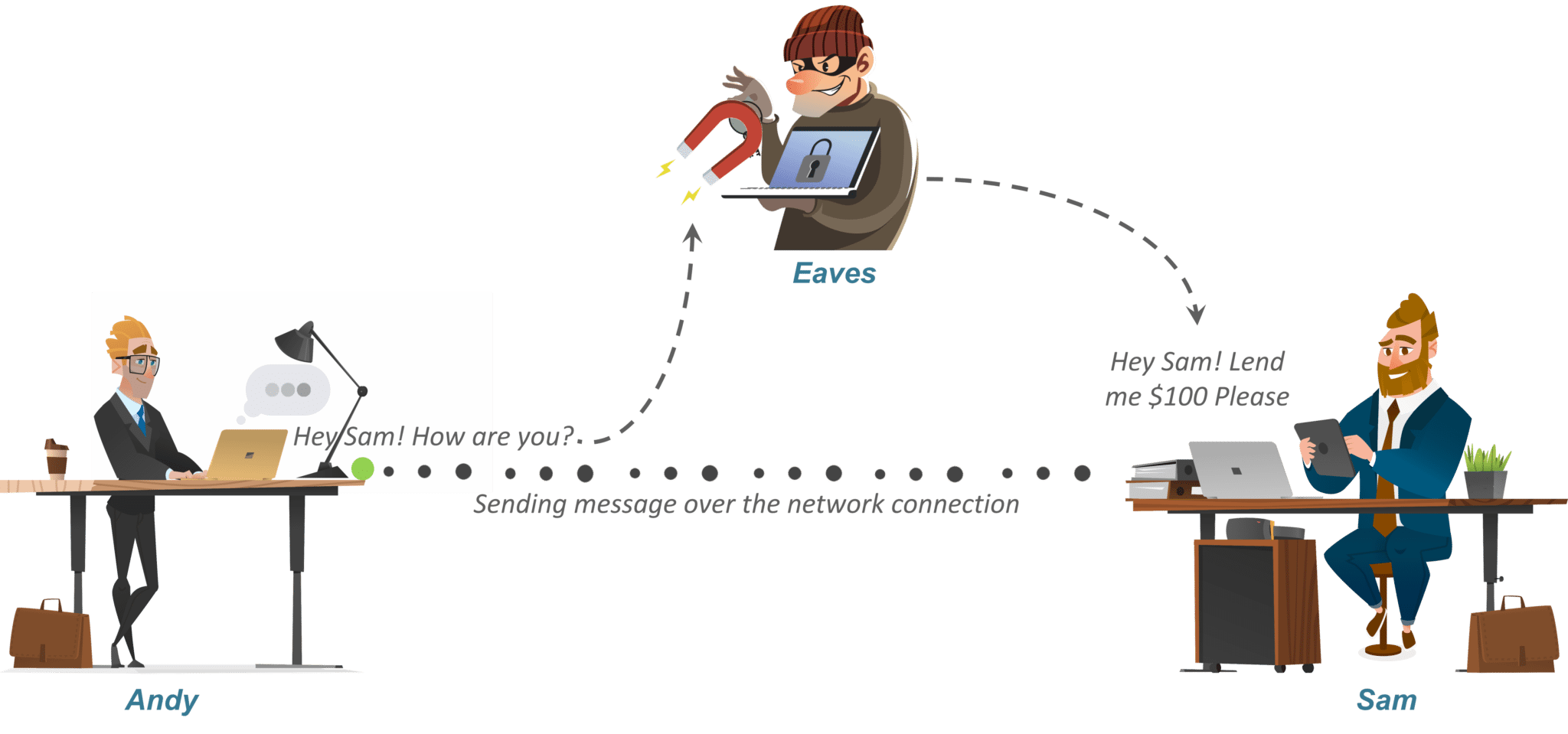
Let’s say there’s a person named Andy. Now suppose Andy sends a message to his friend Sam who is on the other side of the world. Now obviously he wants this message to be private and nobody else should have access to the message. He uses a public forum, for example, WhatsApp for sending this message. The main goal is to secure this communication.
Let’s say there is a smart guy called Eaves who secretly got access to your communication channel. Since this guy has access to your communication, he can do much more than just eavesdropping, for example, he can try to change the message. Now, this is just a small example. What if Eave gets access to your private information? The result could be catastrophic.
So how can Andy be sure that nobody in the middle could access the message sent to Sam? That’s where Encryption or Cryptography comes in. Let me tell you ” What is Cryptography “.
Look out for our CEH V12 Certification Training to learn more about the Ethical Hacking
What Is Cryptography?

Alright, now that you know ” what is cryptography ” let’s see how cryptography can help secure the connection between Andy and Sam.
So, to protect his message, Andy first convert his readable message to unreadable form. Here, he converts the message to some random numbers. After that, he uses a key to encrypt his message, in Cryptography, we call this ciphertext.
Andy sends this ciphertext or encrypted message over the communication channel, he won’t have to worry about somebody in the middle of discovering his private messages. Suppose, Eaves here discover the message and he somehow manages to alter it before it reaches Sam.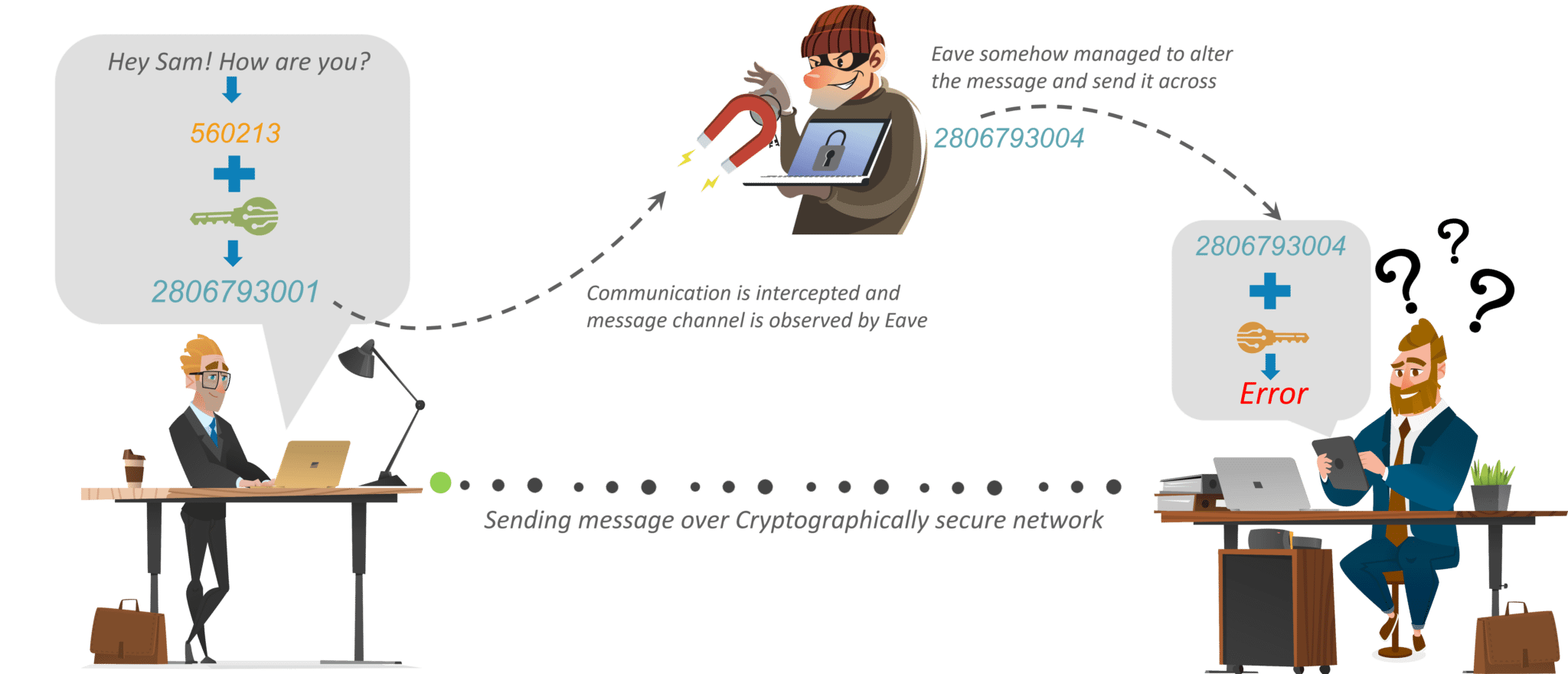
Now, Sam would need a key to decrypt the message to recover the original plaintext. In order to convert the ciphertext into plain text, Sam would need to use the decryption key. Using the key he would convert the ciphertext or the numerical value to the corresponding plain text.
After using the key for decryption what will come out is the original plaintext message, is an error. Now, this error is very important. It is the way Sam knows that message sent by Andy is not the same as the message that he received. Thus, we can say that encryption is important to communicate or share information over the network.
Elevate your cybersecurity knowledge and skills with CISSP Certification Training.
Now, based on the type of keys and encryption algorithms, cryptography is classified under the following categories:
Encryption Algorithms
Cryptography is broadly classified into two categories: Symmetric key Cryptography and Asymmetric key Cryptography (popularly known as public key cryptography).
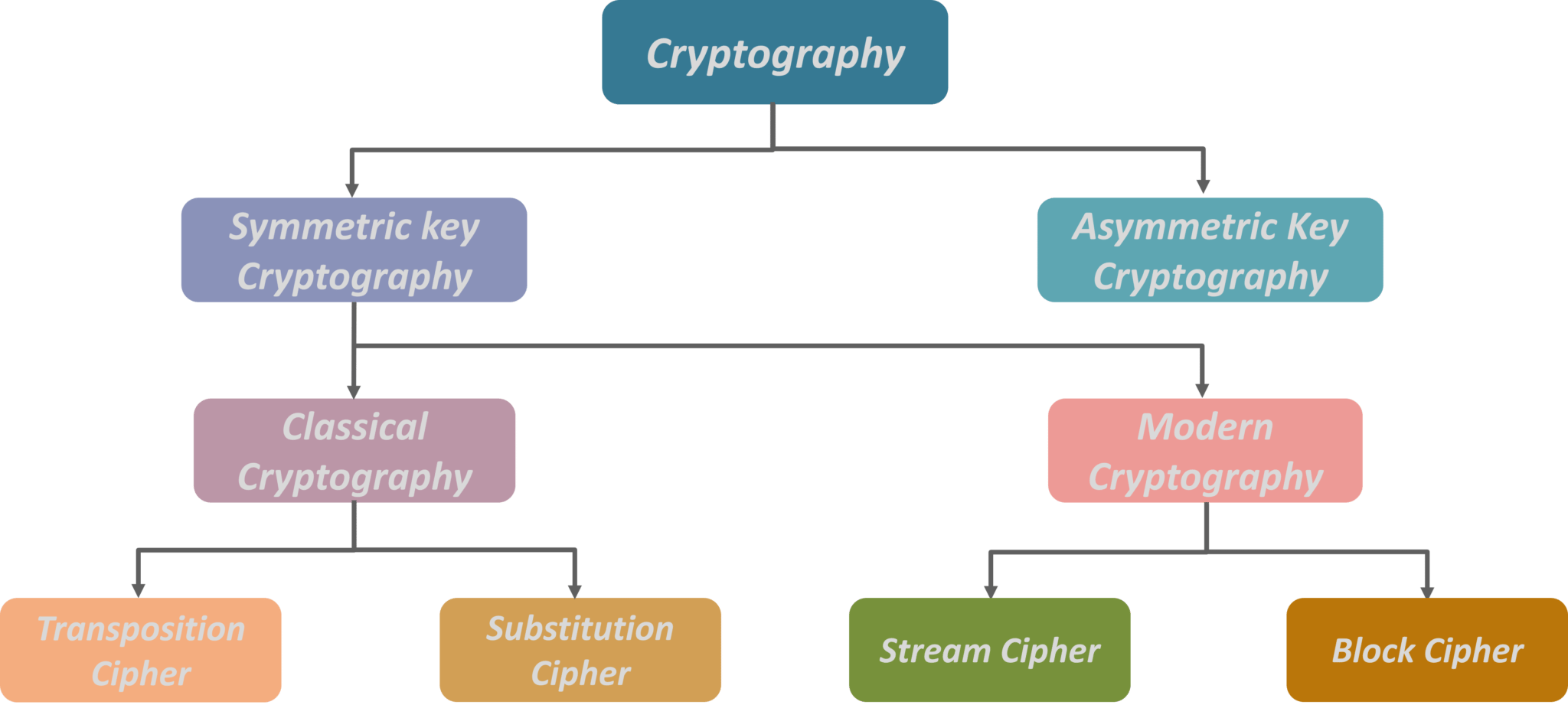
Now Symmetric key Cryptography is further categorized as Classical Cryptography and Modern Cryptography.
Further drilling down, Classical Cryptography is divided into Transposition Cipher and Substitution Cipher. On the other hand, Modern Cryptography is divided into Stream Cipher and Block Cipher.
So, let’s understand these algorithms with examples.
How various Cryptographic Algorithms Works?
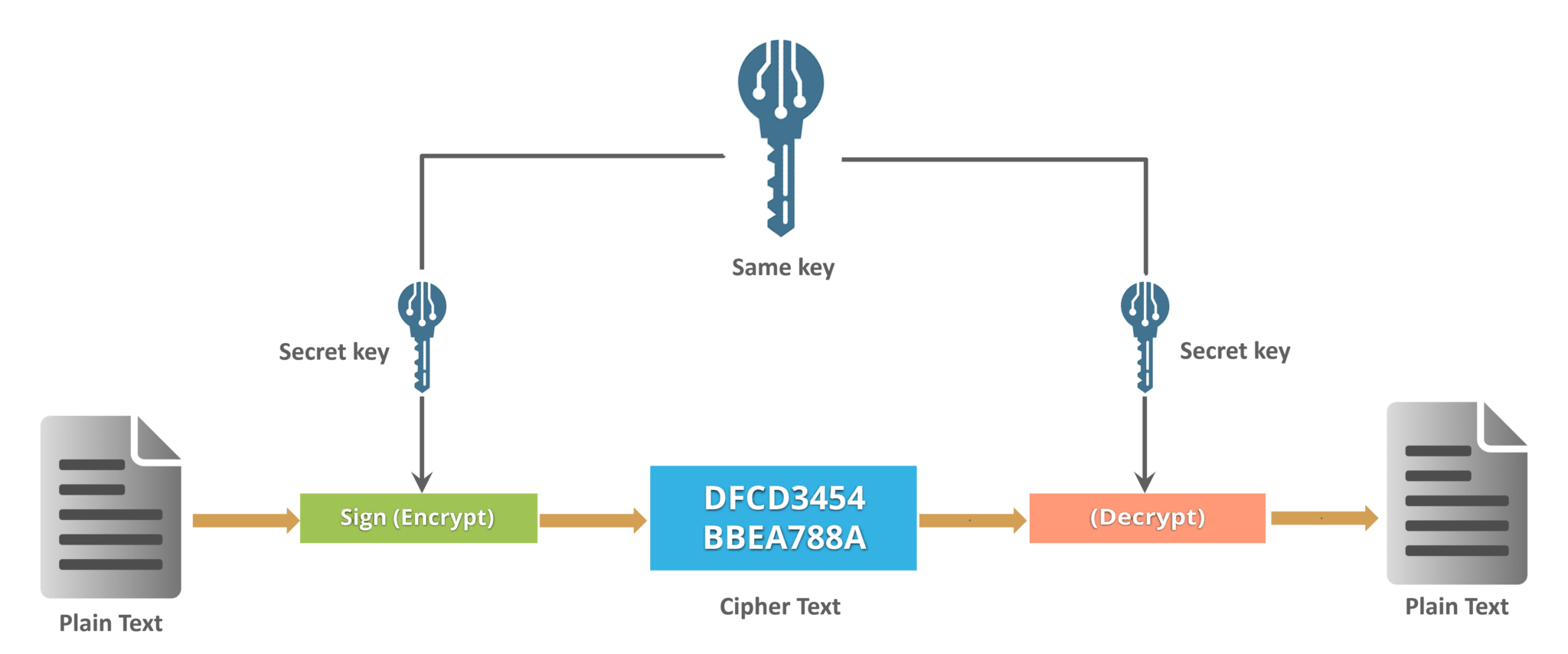
Let’s start with the Symmetric key encryption
Symmetric Key Cryptography
Transposition Ciphers
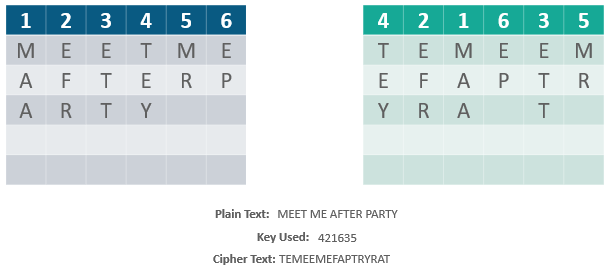
That is, the order of the units is changed (the plaintext is reordered). Mathematically, a bijective function is used on the characters’ positions to encrypt and an inverse function to decrypt.
Example:
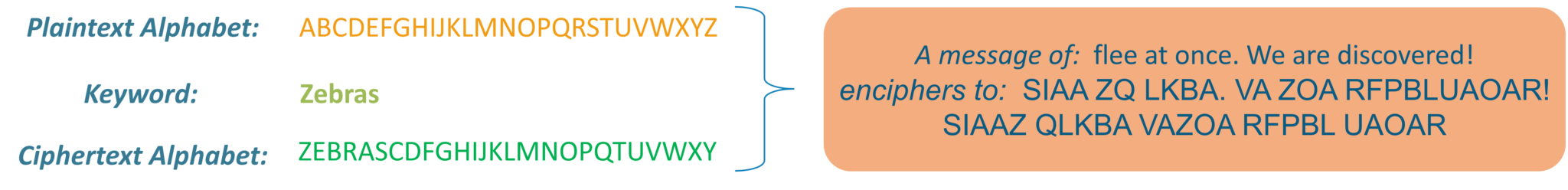
Substitution Cipher
Example:
Consider this example shown on the slide: Using the system just discussed, the keyword “zebras” gives us the following alphabets:
Stream Cipher
Symmetric or secret-key encryption algorithm that encrypts a single bit at a time. With a Stream Cipher, the same plaintext bit or byte will encrypt to a different bit or byte every time it is encrypted.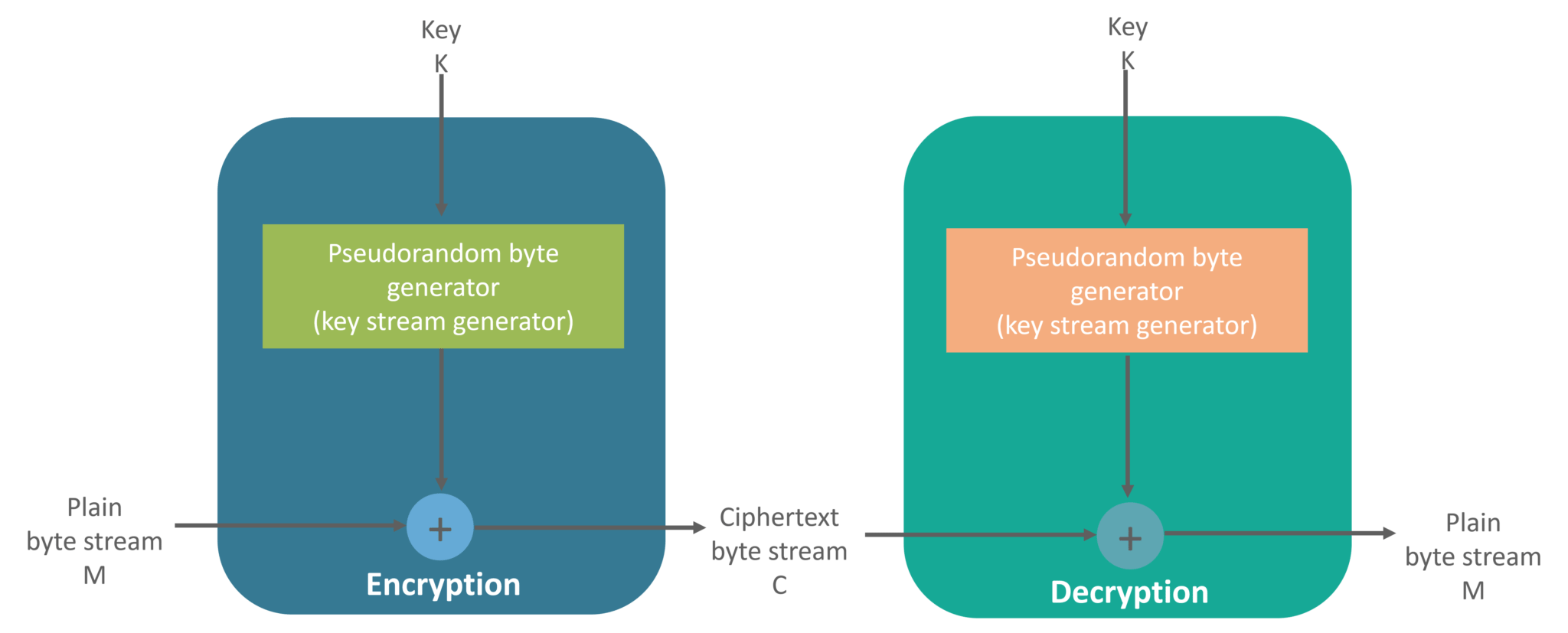
Block Cipher
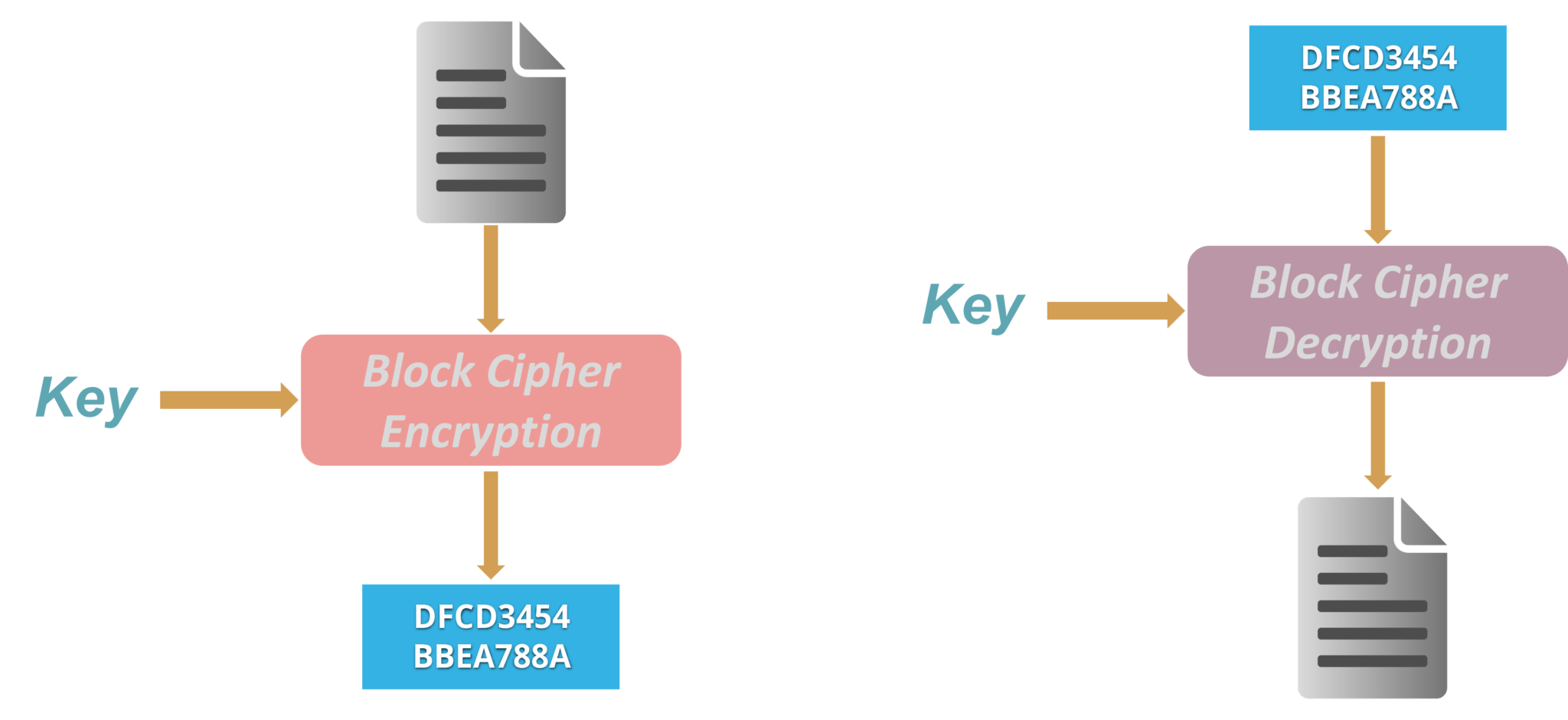
Example: A common block cipher, AES, encrypts 128-bit blocks with a key of predetermined length: 128, 192, or 256 bits. Block ciphers are pseudorandom permutation (PRP) families that operate on the fixed size block of bits. PRPs are functions that cannot be differentiated from completely random permutations and thus, are considered reliable until proven unreliable.
Build a robust Cyber Security portfolio and network of contacts through this Cybersecurity Internship experience.
Asymmetric Key Encryption (or Public Key Cryptography)
The encryption process where different keys are used for encrypting and decrypting the information. Keys are different but are mathematically related, such that retrieving the plain text by decrypting ciphertext is feasible. 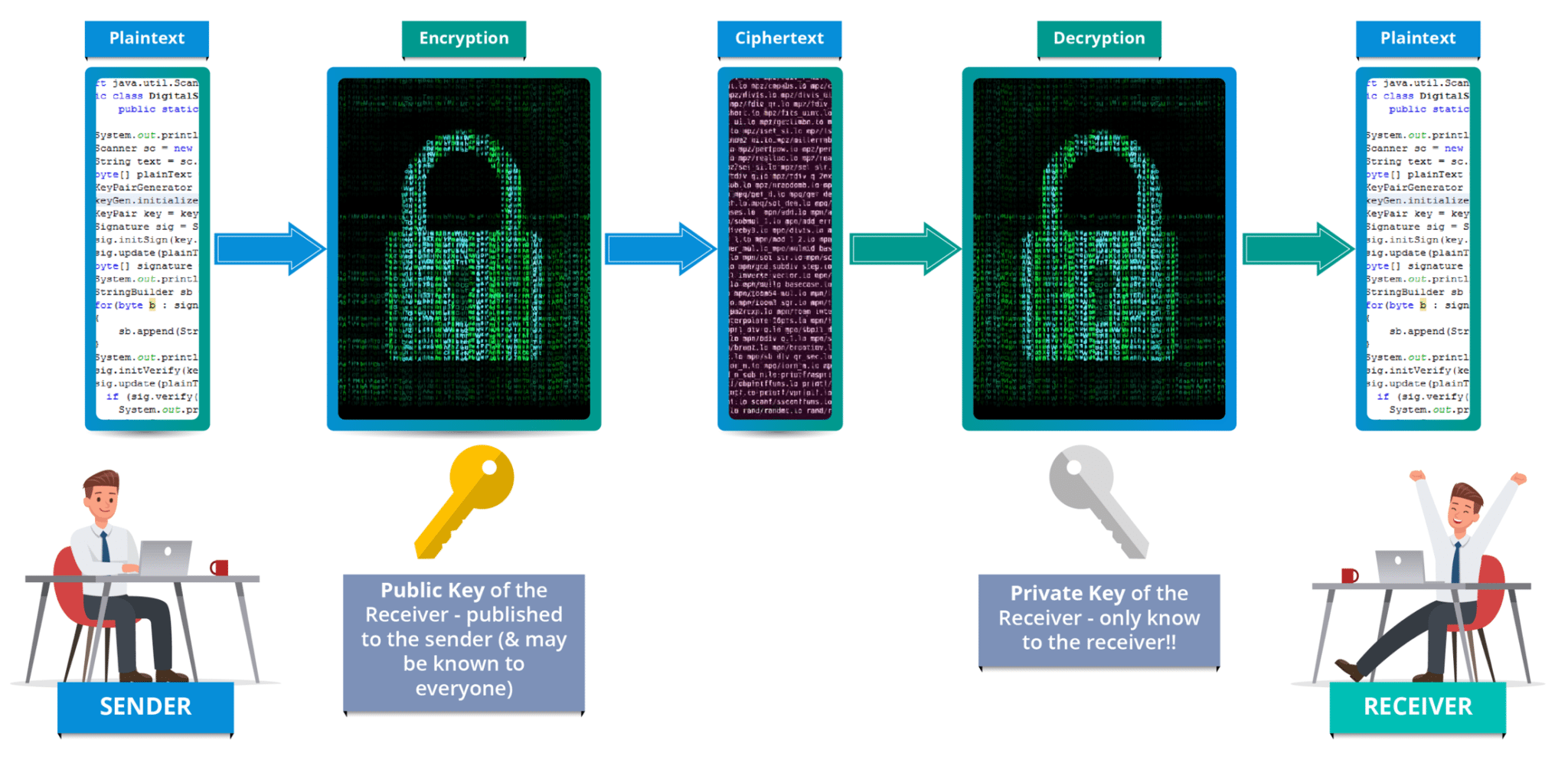
RSA is the most widely used form of public key encryption,
RSA Algorithm
- RSA stands for Rivest, Shamir, and Adelman, inventors of this technique
- Both public and private key are interchangeable
- Variable Key Size (512, 1024, or 2048 bits)
Here’s how keys are generated in RSA algorithm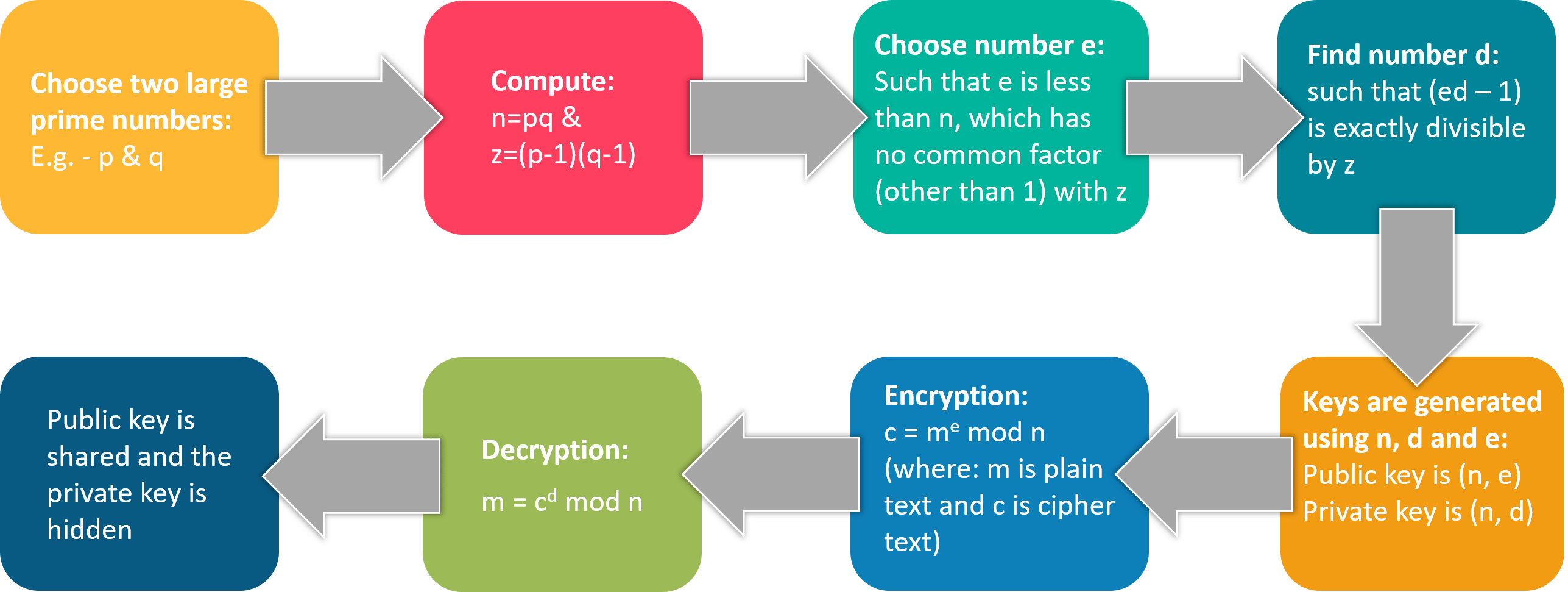
Alright, this was it for “What is Cryptography” blog. To safeguard your information and data shared over the internet it is important to use strong encryption algorithms, to avoid any catastrophic situations.
If you wish to learn Cybersecurity and build a colorful career in cybersecurity, then check out our Cyber Security Certification which comes with instructor-led live training and real-life case studies experience. This training will help you in becoming a Cybersecurity expert.
You can also take a look at our newly launched course on CompTIA Security+ Training Course which is a first-of-a-kind official partnership between Edureka & CompTIA Security+. It offers you a chance to earn a global certification that focuses on core cybersecurity skills which are indispensable for security and network administrators.
Learn Cybersecurity the right way with Edureka’s Masters in Cyber Security program and defend the world’s biggest companies from phishers, hackers and cyber attacks.
Got a question for us? Please mention it in the comments section and we will get back to you.